Microservices architecture: maintaining the customer experience
It is likely that all large companies are already utilising microservices as part of their business strategies. But microservices — small, loosely coupled services that make up a larger [...]
CMM: cyber security beyond compliance
In recent years, 'compliance' has become a bit of a buzzword within the cyber security sphere. However, whilst companies have been concerning themselves with ticking regulatory boxes, they have [...]
Customer IAM: driving the digital ‘high street’ forward
The UK high street has been struggling for some time now. Maplin, Toys R Us and New Look went into administration in 2018, and 2019 told a similar story [...]
Adopting AI: balancing automation with risk management
Artificial intelligence (AI) has already found its way into many mainstream business applications — redefining the modern workplace and unleashing the power of data and automation across a broad [...]
IAM trends: what can we expect from 2021?
If 2020 taught us one thing, it is that you cannot control everything. Sometimes, no matter how prepared you are, an unprecedented event can throw your entire business completely [...]
Has 2020 compromised your business’ cyber security?
This year has seen a lot of disruption, and thanks to COVID-19, businesses of all shapes and sizes have faced increased financial pressures. At the same time, we have [...]
Debunking 7 common cyber security misconceptions
The cyber security industry has grown exponentially over the past decade, with more resources being deployed to counter threats. Yet, a new cyber-attack occurs somewhere on the web every [...]
Risk management: how to secure your AI and machine learning projects
Artificial intelligence (AI) and machine learning (ML) applications have multiplied significantly over the past few years. As they grow in popularity, these tools are increasingly underpinning our everyday lives [...]
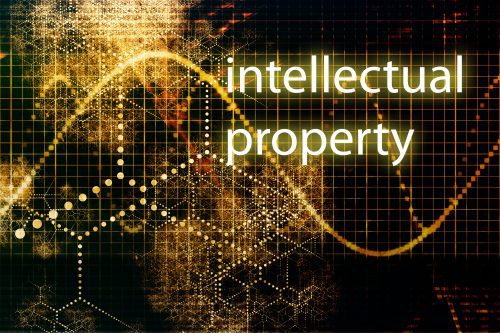
Protecting your company’s intellectual property
Data breaches are a regular feature in the news lately. More often than not, these news stories are concerned with the theft and exposure of customer information. But what [...]
How is your business’ IT security adapting to the ‘new normal’?
For years, organisations have been trying to get to grips with cyber security and figure out how they can protect their systems and network from a breach. Because the [...]
Application security development in the cloud
Application security describes protective measures taken at the application level to prevent data or code within the app from being stolen or hijacked. These measures can include both hardware and software, as well as [...]
IGA: better integration through advanced automation
The importance of Identity Governance and Administration (IGA) in managing and reducing user access risk is well documented. Yet, despite this, many organisations still rely at least partially on [...]
SCADA: keeping your system secure from cyber attacks
SCADA (Supervisory Control and Data Acquisition) is not a specific technology, but rather a type of application that receives operating data about a system to control and optimise it. [...]
IAM: safeguarding organisations against rising cyber threats
Organisations increasingly recognise Identity & Access Management (IAM) as a key enabler and an essential building block for achieving effective business transformation. But what exactly is it? IAM is [...]