IAM: safeguarding organisations against rising cyber threats
Organisations increasingly recognise Identity & Access Management (IAM) as a key enabler and an essential building block for achieving effective business transformation.
But what exactly is it?
IAM is a framework of business processes and information, supported by people and technology, for managing the digital identity lifecycle and system access controls. Within enterprise IAM (inside the company as opposed to customers), it’s about managing the way staff and third parties access systems, based on the roles and attribute-based permissions of the individual. Advanced controls will apply to managing privileged users.
Once an individual’s digital identity has been established, it must then be maintained, modified and monitored throughout each user’s access lifecycle. This lifecycle process is typically driven by the human resources and vendor management processes for new joiners — when a person moves department or function and when the person finally leaves the organisation.
Why is IAM so important?
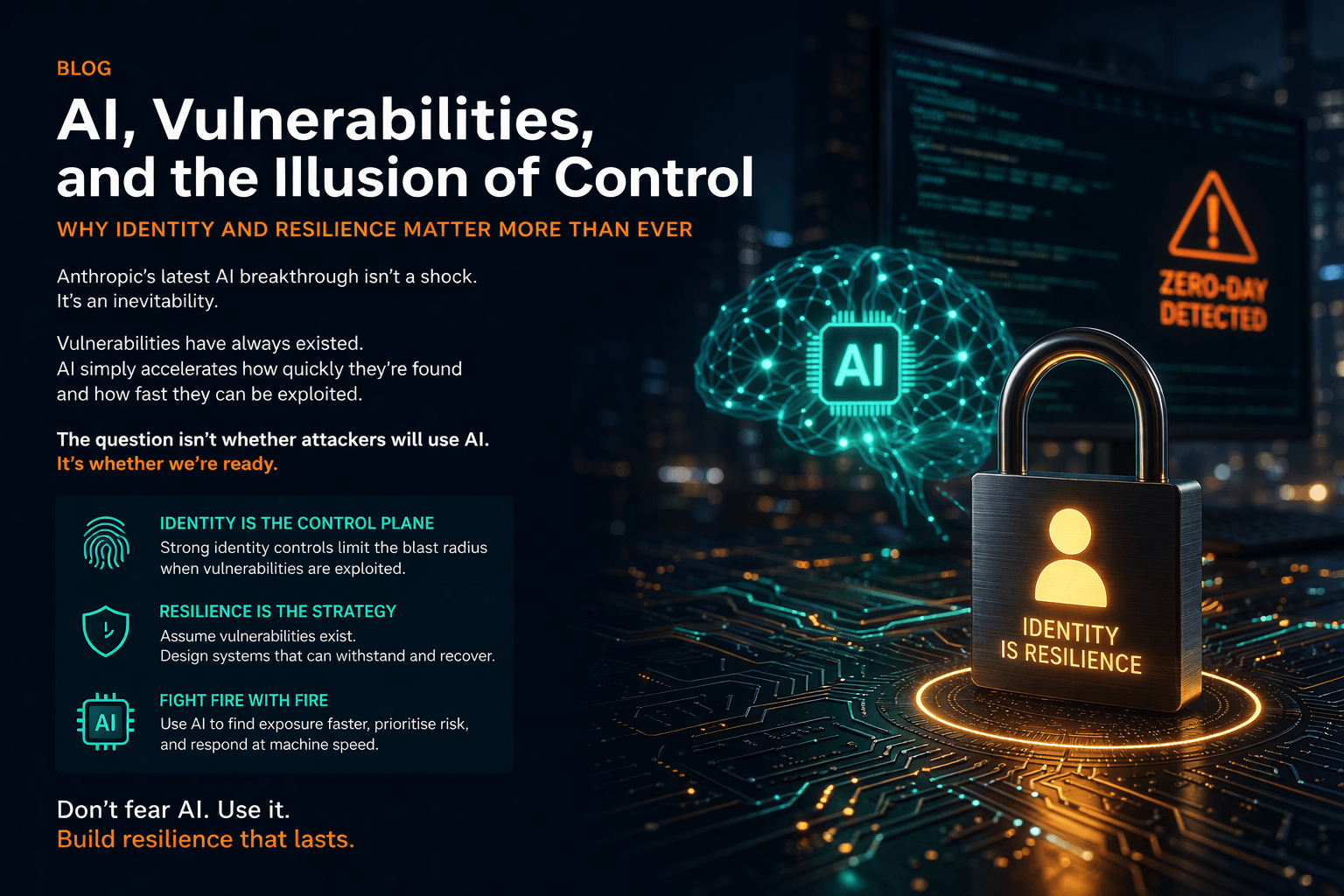
The overarching aim of identity management is to grant access to the right assets, by the right users and in the right context. As the world continues to adopt new technologies and the threat landscape grows, effectively managing identity and access has never been more crucial.
Compromised user credentials can act as an entry point into a company’s network and data. Despite this, users often have more access permissions than necessary. Without a proper control system in place, user information and access rights can quickly become a complex issue to track.
However, over 70% of data breaches are tied to weak or mismanaged credentials, so it’s not something businesses can afford to neglect. A robust IAM system can add a critical layer of protection — ensuring a consistent application of user access rules and policies across an organisation.
IAM allows administrators to identify and maintain user profiles so that they can ensure the appropriate authorisation is granted to information and applications. This maintenance of user profiles can best be achieved through policies and rules imbedded into an Identity & Access Governance (IAG) tool. This ability to control who comes in and out of an organisation’s business and IT applications is vital to securing data and systems.
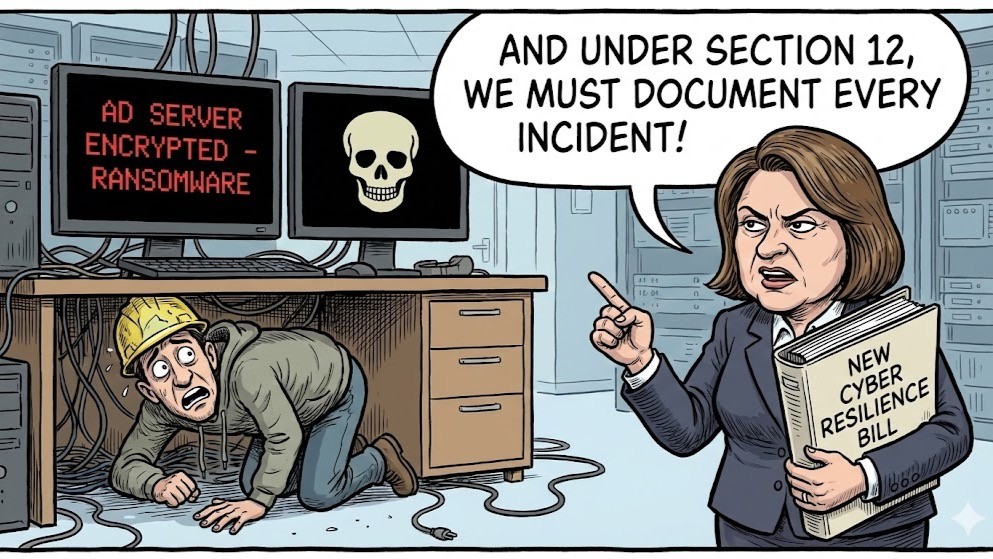
As such, enterprises are increasingly using identity management to safeguard their assets against the rising threats of phishing, ransomware, malware and other forms of cyber-attacks.
A strong password is not enough
In the past, a typical identity management system would have comprised four basic elements: a directory of the personal data the system uses to define individual users; a set of access lifecycle management tools for adding, modifying and deleting that data; a system that regulates user access and enforces security policies and access permissions; and an auditing and reporting system.
Regulating user access has then typically been single factor (such as their username and password) or in some cases, involved various two-factor authentication methods for authenticating. Two-factor authentication combines something the user knows (such as their password) with something they have (a token or smart card).
However, with today’s rising cyber security threats, even a strong password and two-factor authentication are no longer enough. Instead, organisations should adopt a zero-trust approach and look to use multi-factor authentication (MFA) with adaptive user behavioural context. This method of authentication requires users to authenticate with up to three sets of credentials.
Thanks to technologies such as context-aware access control and risk-based authentication delivered through smartphones, today’s identity management systems also offer more advanced user authentication, auditing and reporting at an administration level.
Context-aware access control is policy-based, predetermining an event and its outcome based on specific attributes. For instance, if an IP address isn’t whitelisted, then context-aware network access control might step-up the authentication process and block it.
Risk-based authentication then applies levels of strictness to authentication processes based on the current risk profile. The higher the risk, the more restrictive the authentication process becomes for a user.
Combined with IAG systems, modern MFA solutions will support secure Single Sign On (SSO), self-service and password management for both cloud and traditional network legacy access.
Many IAM programmes struggle to balance the need for immediate improvement with long-term effectiveness. This is why it’s essential to align the design, architecture and delivery of identity solutions to an organisation’s change management objectives — while ensuring the core controls map directly to broader security, risk and audit management processes.
Want to know what the top IAM challenges are and how we’ve helped our customers solve them? Download your free copy of ‘IAM Top 10 Challenges’ today.