Improving post-pandemic cyber security: identity and access management
A lot has changed in the cyber security industry over the past few years. The pandemic instigated an unprecedented shift towards digital processes, with more and more people turning to technology to support daily functions.
Unfortunately, with all the advantages of technology comes the increased risk of cyber attacks. The cyber security industry has widely reported that the threat landscape has worsened dramatically since organisations worldwide embraced digital transformations. And as cyber criminals assume progressively sophisticated methods to target victims, individuals and businesses are even more vulnerable to a breach.
We recently examined our clients’ Capability Maturity Model (CMM) assessment reports to identify trends across different elements of cyber security in the post-pandemic world. Our last blog outlined the generic findings from the assessments and the impact of COVID-19 on domains and planned capability and maturity gains.
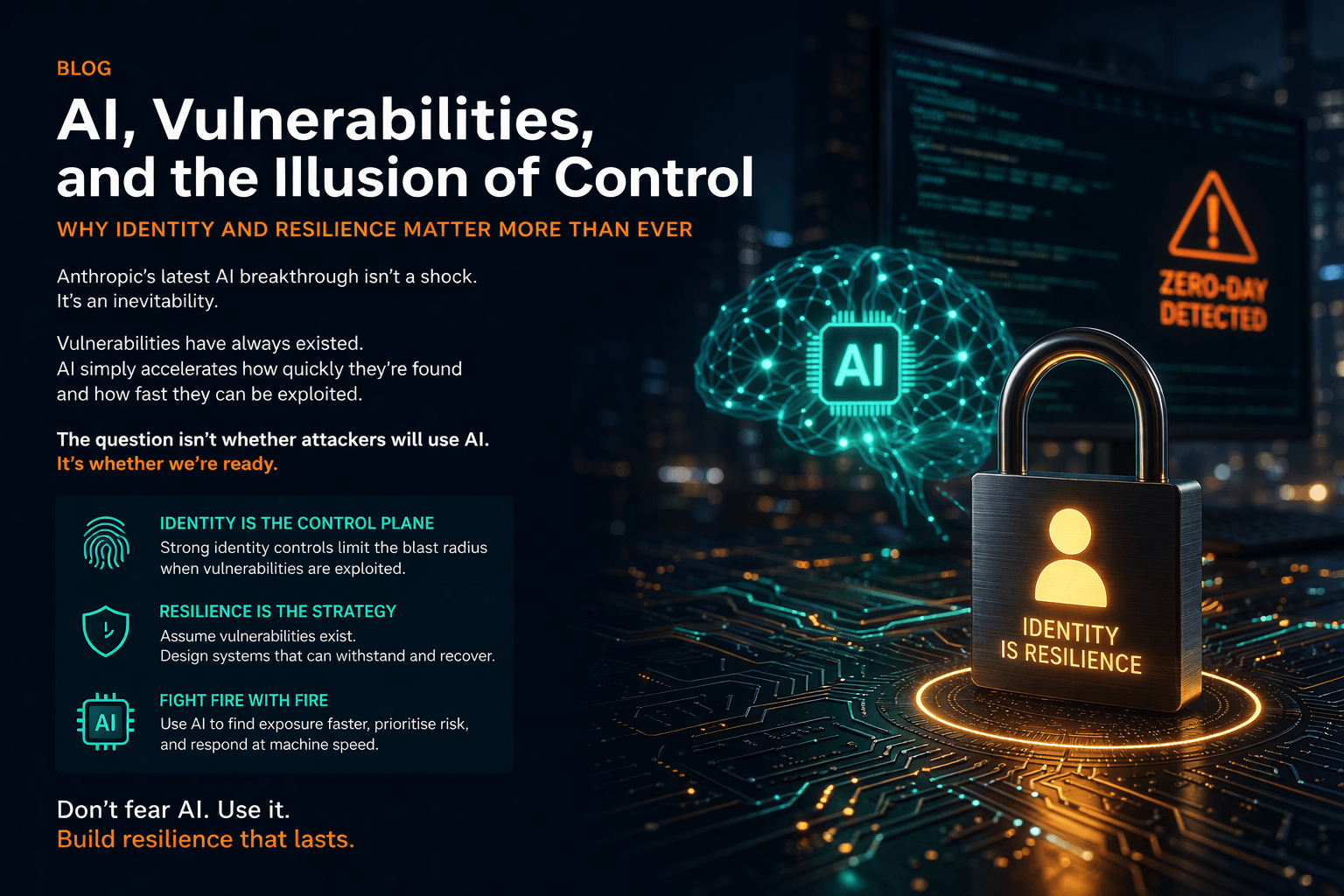
This month, we have analysed another key theme from these reports: the importance of identity and access management (IAM). Our findings revealed that most of our clients see IAM as a priority, with a number of them making changes to their processes as part of security transformations in the post-pandemic world.
What is IAM?
Identity and access management is a discipline for managing electronic and digital identities, authentication and access rights. The objective of an IAM strategy is to effectively define and control the roles and access privileges of individual systems users and devices.
An IAM system stands between users — ranging from system accounts and bots (a computer program that operates as an agent for a user or other program) to business partners and employees — and critical assets, preventing unauthorised personnel from gaining entry to a system via compromised passwords and user identities.
Within an IAM framework, various processes, policies, and technologies facilitate application and infrastructure security by ensuring only authorised users have access to company resources. Industry 4.0 technologies like artificial intelligence and machine learning enable solutions such as multi-factor authentication (MFA) and cloud-based identity as a service (IDaaS) infrastructure to track malicious behaviour and alleviate security risks associated with unauthorised systems access.
Aside from the apparent benefits of cyber security, IAM has several other advantages for organisations. It can ensure compliance with government data security regulations, boost productivity by automating access controls and optimise user experience using single sign-on (SSO) and other IAM tools. Plus, complex legacy authentication and authorisation methods can be removed and aligned to industry standards, thereby underpinning digital modernisation programmes. So, IAM is an essential component of any up-to-date security programme.
Access controls are more important than ever
Our research has shown that the importance of IAM has grown for our clients in recent years. The pandemic drove swathes of businesses to adopt cloud technology to enable remote working and prevent business collapse during lockdowns, causing the number of digital identities requiring monitoring and managing to explode.
As such, most of our customers are striving to make significant changes and improvements to their IAM processes. We recommend implementing a zero-trust network with a ‘least-privilege’ approach to identity security, which involves assigning access rights only where needed and for the shortest possible time.
Senior employees and administrative staff are likely to possess high-level authorisation, creating dangerous weak points for enterprise systems security. Privileged access management, or PAM, is an information security mechanism that falls under IAM. It is designed to monitor privileged access to accounts and applications and protects identities with priority access that are prime targets for cyber criminals.
Now that hybrid working and outsourcing pressures have added greater risk to the threats posed by company insiders, both knowingly and unknowingly, privileged account management is more critical than ever. Nearly all our customers have mature processes for managing privileges in accessing operating systems and database access. However, there are gaps across many companies when handling the privileges assigned to applications, cloud services and bots. If your company does not effectively manage privileged access, it is falling behind the curve in the current climate.
Customer identity and access management is critical
Customer identity and access management, otherwise known as CIAM, is another component of IAM that stood out from our client reports.
Coronavirus lockdowns amplified the convenience of consuming or shopping online, changing the ways businesses engage with online customers. The pandemic led them to leverage advanced access control systems to attract customers and build relationships in the traditionally impersonal online environment. As more companies and private consumers buy online, the risk associated with account takeover attacks and the benefits realised with risk-based authentication have driven many of our customers to modernise their CIAM environments.
Through CIAM solutions such as integrated personalisation, SSO, consent management and adaptive authentication (with MFA), businesses can capture, monitor and maintain customer profile data to improve security and user experience when navigating services and ordering or shopping online. These are essential considerations for business leaders in the digital world, where ensuring data security and a ‘frictionless’ user experience is integral to securing digital transactions, compliance and customer retention.
Next month, we will outline technological innovation and the increasing threat landscape in part three of this blog series about cyber security in the post-pandemic world. For more information about how Burning Tree’s information security consultants can keep your business’ systems safe, contact us at 01252 843014 or email info@burningtree.co.uk.