Contextualising post-pandemic cyber security: maturity gains and domain changes
The landscape of cyber security has changed dramatically over the last few years.
In the wake of the pandemic, technological innovation and rapid digitisation have led businesses to embrace digital transformation at an unprecedented pace. However, the implementation of security controls has not always followed suit, leaving many systems vulnerable to the growing threat of a cyber attack.
The process of achieving cyber security maturity takes time, yet few businesses have the necessary protocols in place to effectively prevent a breach in the face of sophisticated scams. And with the likelihood of a cyber attack having significant financial, legal and reputational repercussions for victims increasing, business leaders must act now to protect their organisations.
We have examined our clients’ Capability Maturity Model (CMM) assessment reports to identify trends across different elements of cyber security, such as the impact of COVID-19 and remote working on maturity gains and new capabilities introduced in the post-pandemic world. The insights these reports provide will help determine how and why businesses are affected by recent changes in the industry — and what businesses leaders must do to mitigate against the growing threat of cyber crime.
How has the pandemic disrupted planned capability and maturity gains?
Something that stood out across this set of assessment reports is that the pandemic interrupted clients’ planned initiatives, which, in turn, impacted maturity gains. Repeated investment re-baselining, changes to the threat landscape and delivery constraints resulted in reshuffled priorities during the COVID crisis, with ‘normal’ cyber security initiatives falling down the list of urgent actions.
To conform to ISO 27000 standards — a series of best practices published by the International Organization for Standardization to help organisations improve their cyber security — businesses must demonstrate information security maturity within the principle of continuous improvement. Plus, maturity helps manage security improvement programs and keep risk within acceptable levels — no different from other security standards such as Good Practice or NIST.
However, our findings suggest an inverse correlation between security control efficiency and acceptable risk levels. As a result, very few organisations attain — or even target — the highest maturity rating. The highest levels of maturity are best described as automated and risk-appropriate. While this is a good aspiration, improvements in information security maturity are often changes that can face significant impediments, and more often than not, these challenges result from cultural obstacles. In some industries and for specific security domains, automation and risk-appropriate decisions come with a price tag that just does not make sense.
Our reports found a lack of cyber awareness in several organisations, an underestimation of the importance of security efforts from the top down and a lack of incentives for improving and rationalising information security. A clear-sighted understanding of a business’ information security posture, balanced against an understanding of its needs, can help overcome these cultural obstacles, justify expenditures, and raise awareness of the importance of information security.
How has remote working instigated domain changes?
Assessing an enterprise’s maturity level enables companies, security professionals and risk managers to reduce the deficiencies in existing security measures and set the optimum acceptable risk target. Using the CMM, we assess organisations’ cyber security capabilities and their progress towards achieving security improvement goals.
Our client assessment reports revealed the impact of changing working models in the wake of the pandemic on various areas of organisations’ cyber security.
Ensuring information security for business continuity management (BCM)
Covid presented significant tests for BCM systems — which manage risks to critical business functions to ensure service continuity during a disruptive incident — with organisations forced to adjust quickly to home and hybrid working conditions.
Implementing an effective cyber security system is imperative for a range of information security aspects of BCM resilience, ensuring organisations conform to requirements such as the GDPR (General Data Protection Regulation) or the NIS Directive (Directive on Security of Network and Information Systems). Some customers’ BCM systems stood up well against the challenges the COVID-19 crisis presented. Those that did not quickly become proficient suffered unequally with a more significant number of security incidents.
Maintaining physical and environmental security in hybrid working models
Coronavirus had an interesting impact on information security aspects of physical and environmental security protocols that prevent unauthorised physical access and damage to organisations’ information and information processing facilities.
Some traditionally office-based customers are scaling back as the importance of in-person working has diminished. In contrast, clients who have decided to implement new hybrid working practices permanently have a whole new set of risks to consider as people return to the office more inconsistently. Companies in sectors that depend on their physical working spaces — such as manufacturing or retail — rapidly stepped up their systems’ maturity to accommodate environmental conditions imposed by the pandemic.
Supporting the information security aspects of human resources
Human resources security has stepped up in some organisations thanks to improved security awareness and contract management. However, other HR departments have been too busy adapting other operating procedures to manage information security effectively.
Information security organisation is more challenged than ever before, with an already stretched market struggling for resources due to Brexit, the pandemic and increasing threats — not to mention a considerable amount of stress on security staff. Some businesses identify existing personnel and start training programmes to create resources, but this risks newly qualified security professionals moving on for higher salaries. So, many organisations consider outsourcing or buying cloud computing software and services to alleviate staffing pressures.
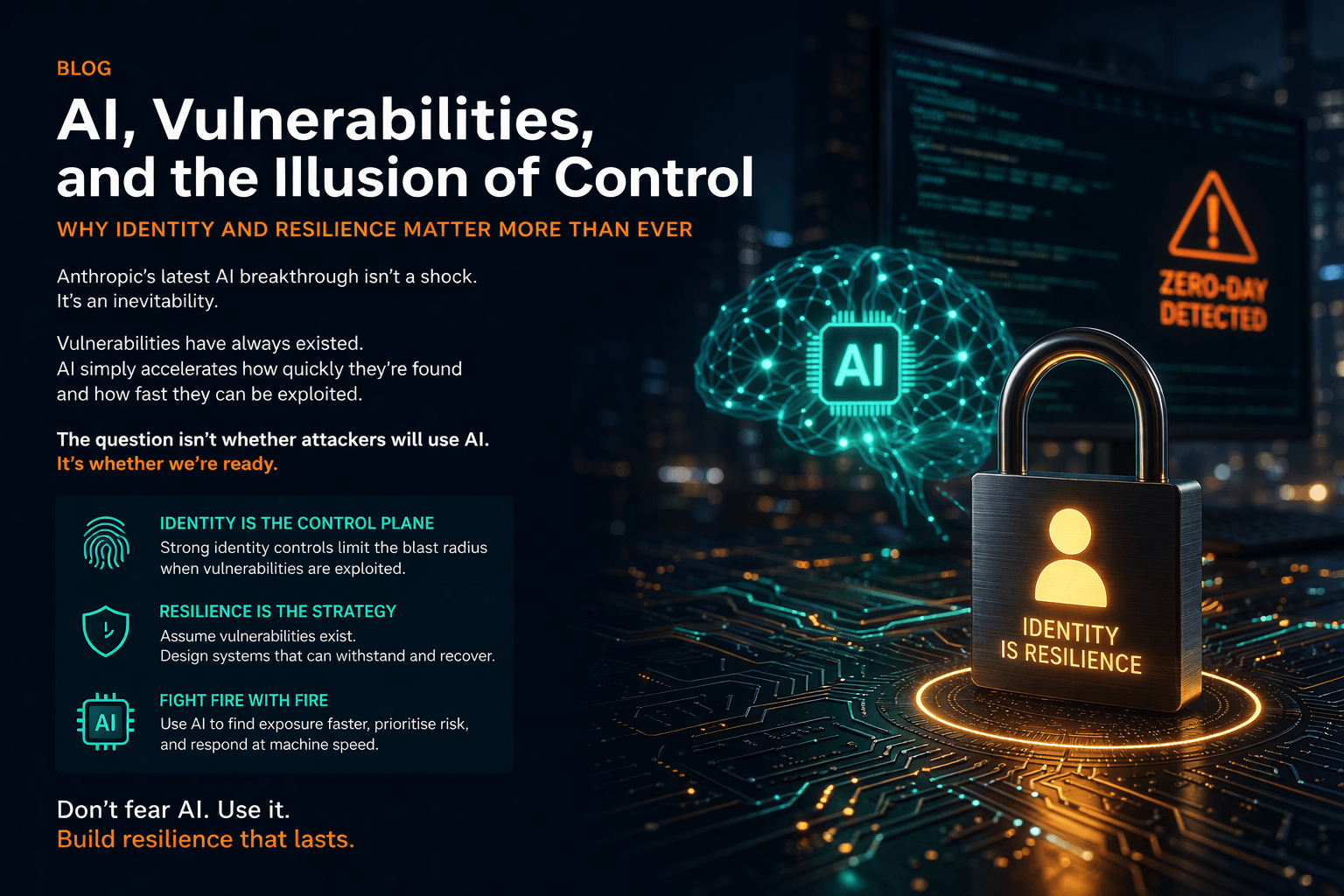
This blog is the first in a three-part series outlining the recent findings from our analysis of client assessment reports. Next month, we will be looking at the impact of the pandemic on identity and access management.