Reinforcing post-pandemic cyber security: adapting domains
As more data goes digital and companies worldwide embrace technology and automation to accommodate remote working and improve operational efficiency in the wake of the pandemic, IT systems face new risks.
From employees working on vulnerable home networks to cyber criminals launching a barrage of phishing attacks, cyber security teams have their work cut out to keep up with the ever-changing threat landscape.
As a result, insights from our clients’ Capability Maturity Model (CMM) reports have revealed a few key areas where domain changes have been implemented to ensure data is secure and critical systems continue to function smoothly.
Domain changes driven by risk and the ever-increasing threat landscape
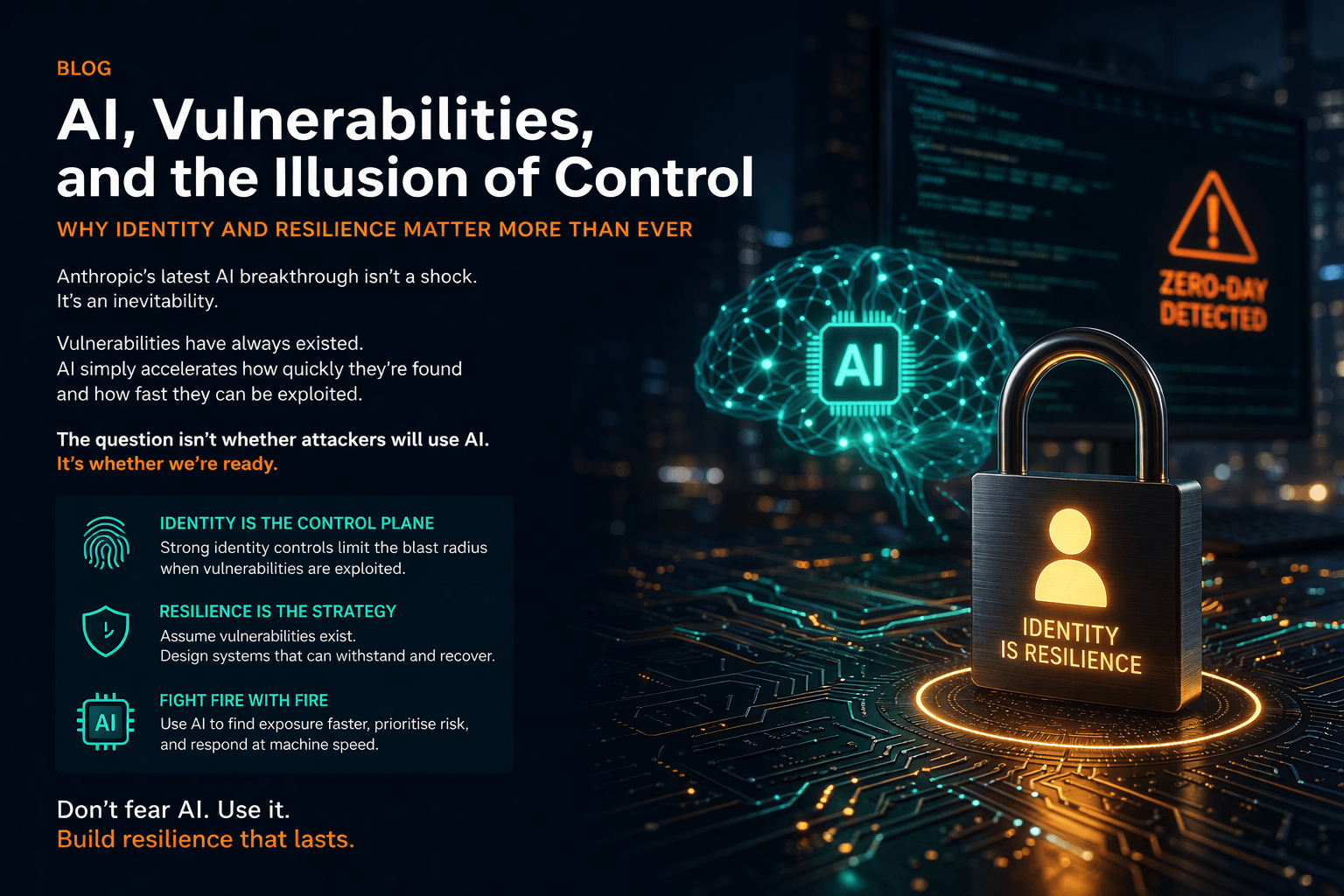
Our research has shown that COVID-19 has impacted planned capability and maturity gains and highlighted the importance of identity and access management (IAM). Additionally, we have found that cyber security domains are constantly changing alongside digital transformations as the industry expands to meet continually evolving cyber threats.
In cyber security, a domain is a group of devices or networks that share the same security protocols and access rights, functioning under the umbrella of security disciplines such as IAM or communications security.
Security operations, also known as SecOps, combine IT operations practices and internal information security to facilitate seamless collaboration and reduce risks. This methodology varies significantly between organisations. Still, the findings from our CMM reports suggest that current operational processes are dominated by incident management and supporting change in other domains.
For example, data encryption is a fundamental building block of cyber security and the simplest way to ensure unauthorised users and malicious actors are unable to read stolen information. As such, encryption has become a default ‘always-on’ control for many customers, with others driving towards adopting such a strategy.
Our research also emphasised that security incident management has been stretched to its limits in confronting increasing attacks, viruses and disruptive actors. So, ‘fighting fires’ has been the order of the day, with security improvements limited to optimising rules and implementing cyber security data science to reduce the volume of threats.
As a result, we have encouraged more use of technology such as artificial intelligence (AI) to enhance and automate the identification of unknown risks.
Domain changes driven by disruptive technologies and innovation in security
According to our clients’ CMM reports, our customer base is also turning its focus towards automation to achieve cyber security maturity.
Modern technologies such as AI, cloud computing and the internet of things (IoT) have allowed more businesses to upgrade their technological capabilities and streamline their systems, creating a more connected and efficient world.
However, with more data being stored and exchanged online, cyber criminals have more opportunities to breach vulnerable IT systems. Consequently, in the wake of these challenges, the cyber security industry is constantly developing security tools and processes designed to detect, identify and address the risks facing businesses’ IT systems.
System acquisition, development and maintenance policy is shifting towards a more agile way of working, delivered by Development Security Operations (DevSecOps) models that embed continuous security testing into DevOps: a set of practices that combines software development with IT operations. Retraining in this space will be critical for businesses wishing to mature security.
Businesses have also adjusted their supplier relationships to support ‘anything-as-a-service’ cloud models such as software as a service (SaaS), as customers seek more flexible subscription-based technology. Vendor risk management is dominating the discussion at this level.
Additionally, new approaches to communications security favour zero trust models with less reliance on network perimeters. In its simplest form, zero-trust security involves every user, device, service or application in a connected network going through IAM authorisation to gain a least-privileged level of access entitlements. This ‘never trust, always verify’ approach will be essential for providing layered threat protection and robust authentication methods during digital transformations.
To learn how our information security consultants can ensure your systems keep pace with the changing threat landscape, contact us at 01252 843014 or email info@burningtree.co.uk.