Zero trust: enabling business continuity and security during a pandemic
From business owners and management staff to IT support and security teams, more people than ever are now working from home due to the coronavirus outbreak.
As a result, many companies are starting to realise their ageing systems with a limited number of connections are no longer up to the task. Organisations are also struggling to ensure staff continue to use systems securely while working remotely.
We recently warned of a rise in cyber criminals exploiting the pandemic and taking advantage of the increasing amount of time people are spending online. However, as we highlighted in our blog, security not only concerns itself with stopping the ‘bad guys’ but also making sure that only the authorised staff can access systems.
At Burning Tree, we’ve found that customers who have adopted cloud technologies and implemented a zero-trust architecture within their business have adapted more seamlessly to the current situation.
What do we mean by ‘zero trust’?
The seeds of ‘zero trust’ were first planted in 2004 by the Jericho Forum, which wanted to explore the potential to develop common security architectures to support the de-perimeterisation of networks. These early predictions can be seen in many industries today, with hybrid networks across all sectors.
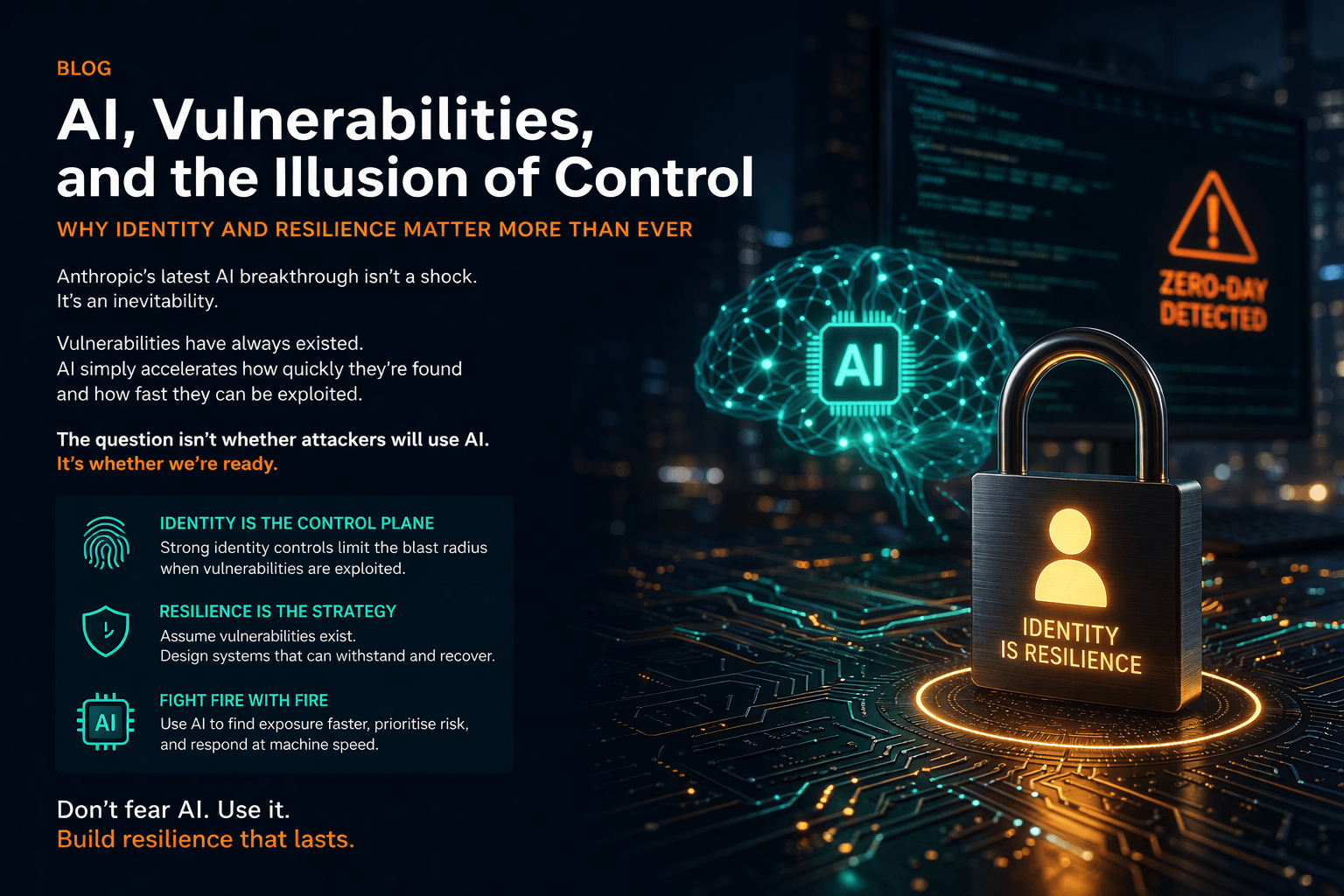
In its simplest form, ‘zero trust’ means that nothing is trusted in itself. Every user, device, service or application is connected — glued together by the network. As such, every single user, device, service or application is implicitly untrusted and must go through a robust identity and access management process to gain a least privileged level of trust and associated access entitlements.
The latest security buzzword
Though the principles of zero trust are largely unchanged, the security network perimeter has disappeared, and the complex threat landscape is ever-evolving.
Many organisations are still using legacy applications and identity systems — which focus on the person only and are not built for the zero-trust model — or access control systems which lack contextual analytics.
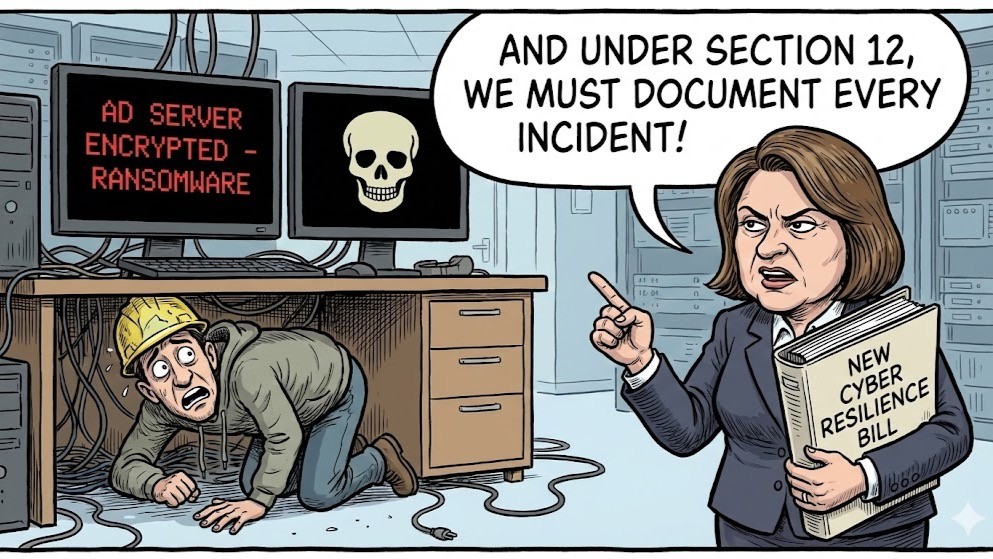
North-South packet inspection and zone-based firewalls are no longer good enough. Network access control (NAC) is no longer practical due to trust erosion and the inconsistency of devices and applications. Where statistically the majority of threats were internal, now they come from the outside, too. The current coronavirus situation has also put a real strain on traditional VPN access, as entire workforces are required to work from home.
Vendors have caught onto the enormity of the problem, and many are investing heavily in anticipation of demand. Unfortunately, this increased demand also means ‘zero trust’ has become the latest security buzzword — making it significantly more difficult for companies to position security changes and technology investment.
Much of what we are seeing in this area is driven by emerging technology and business trends. Privacy and data protection following GDPR are still at the forefront — but disruption, innovation and change are the new norm. However, there is still a growing need for cyber security to become more proactive and user friendly.
Establishing zero-trust architecture
To help you make the right security decisions and demystify the topic, we wanted to break down some of the steps and applications involved in implementing a zero-trust approach.
DevOps and microservices are fast becoming the standard, with imbedded security meaning ‘DevOps’ is now changing to ‘DevSecOps’. Modern cloud-enabled applications are increasingly being developed according to security standards such as OWASP Top Ten, while digital authentication credentials and privileged access are being managed through vaulting passwords.
Zero-trust architecture is established when network, application and identity and access management (IAM) co-operate to protect corporate data.
Zero-trust networking (ZTN) is one component of an end-to-end zero-trust model. It focuses on the IP network where all network traffic is considered untrusted. For ZTN to be effective, every session must first be authenticated, authorised and accounted for before communication is allowed to be established. ZTN enforces security policies at the edge of networks and stops malicious traffic at its origin — not in the middle of the network or at the front door of an endpoint or application.
However, the endpoint needs to be authenticated as much as the individual. To manage this in the world of PCs, laptops, tablets, smartphones — even gaming platforms and smart TVs — authentication needs to have adaptive and context-based capabilities to create a signature for users. Employing step-up and multifactor authentication will help to strengthen this trust, while the use of identity as an application programming interface (API) can improve reliability and reduce fraud.
IAM is then the glue to establishing trust. The classic IAM solutions (such as employee perimeters with federated access) are no longer effective. While these systems can be leveraged to manage the identity lifecycle of employees, it is the access framework that needs to incorporate the appropriate functionality to maintain trust.
Trusting the technology
Getting your zero-trust architecture right will deliver great benefits and allow your computer-based workforce to work from anywhere, at any time, using any device — and more importantly, to do so securely. Burning Tree can help demystify the hype and apparent complexity of zero-trust to help you realise these benefits.
We offer a range of consulting services and work with our partners to provide a range of identity management, access control, network security and secure application development solutions.
To help establish a zero-trust solution, technology can be broadly divided into three main groups:
- Access control: One Identity, Clear Skye, Entrust Datacard, Okta and Twillio
- Network control: Cyglass and Fidelis
- Application control: aapi and CyberInt
If you would like to find out more about zero-trust architecture and how you can implement this approach into your business, please contact us today.