iC Consult: a holistic approach to access management
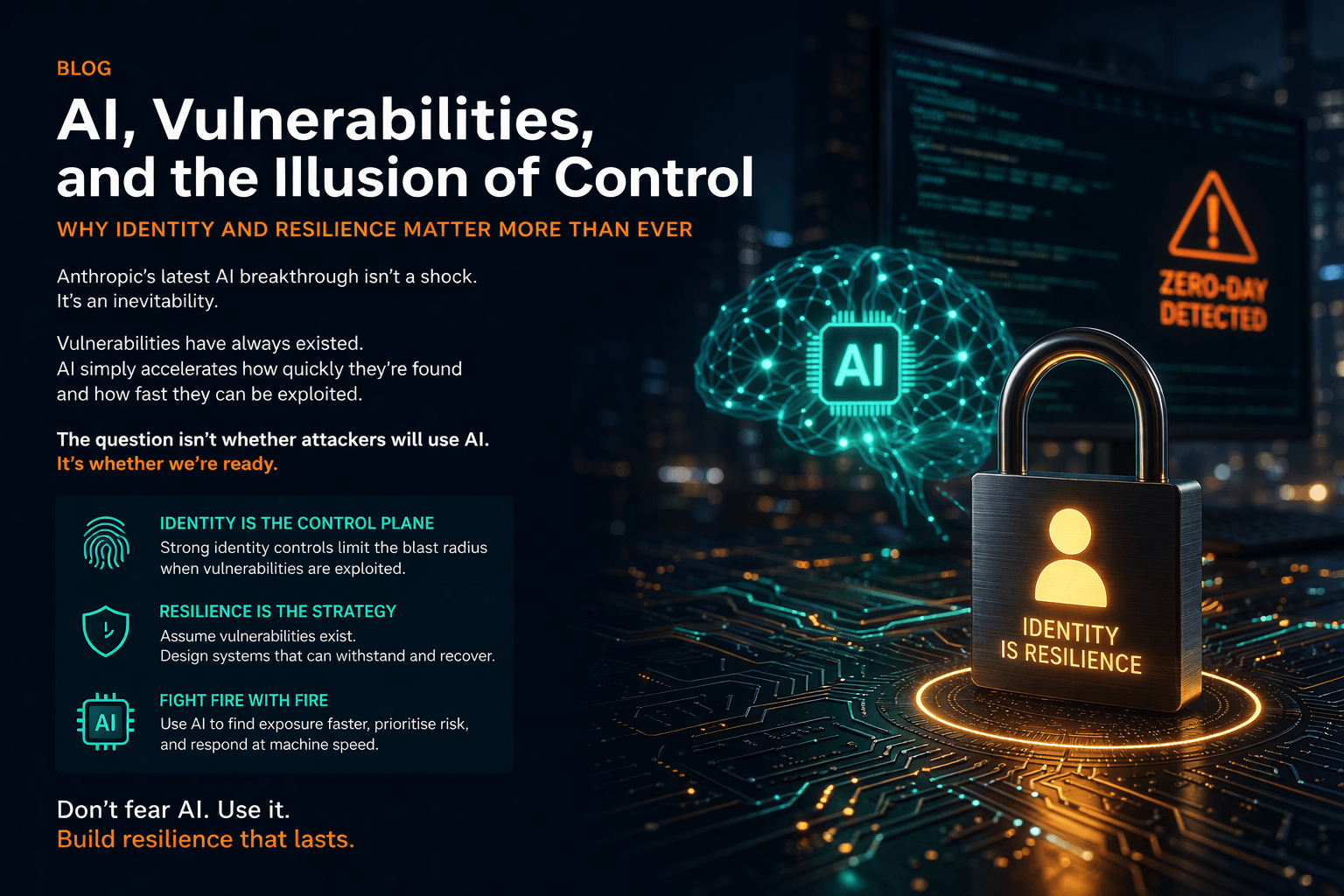
IT security and Identity and Access Management (IAM) have not looked the same since the pandemic, which prompted the rollout of remote working and accelerated digital transformations.
With the volume of data being shared and stored via the cloud constantly growing, on-premises IAM solutions alone can no longer keep systems secure. Instead, a more holistic approach to IAM is required to effectively manage all identities in a system and mitigate the risk of a breach.
At Burning Tree, we work with several experienced technology and software partners to provide our customers with solutions for their particular security needs. One such partner is iC Consult: the world’s leading vendor-independent systems integrator and managed services provider specialising in IAM solutions for large organisations.
iC Consult’s solution packages provide a 360° view of the entire IAM lifecycle, developed with specialist vendors to provide customers with a forward-thinking strategy that ticks every box.
The solution to complex IAM challenges
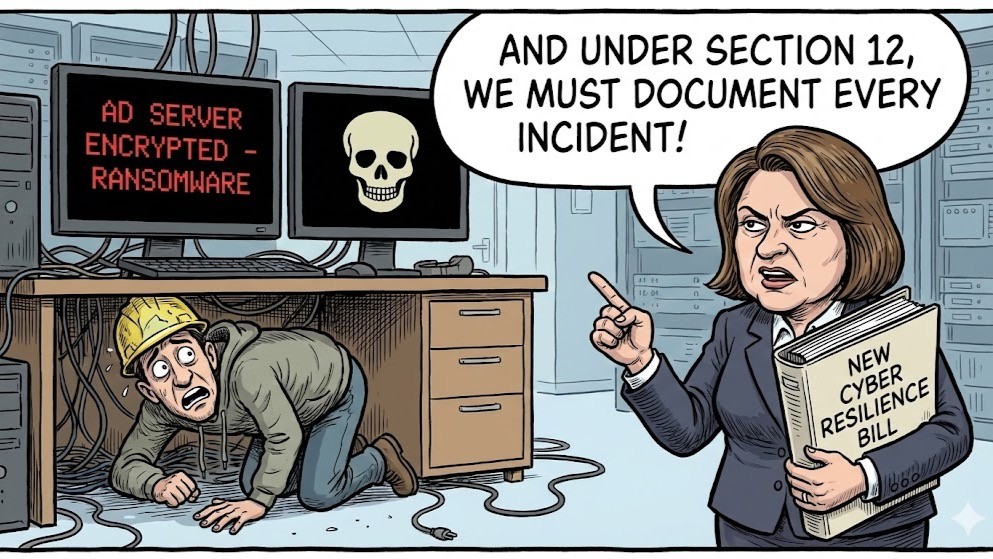
Investing in IAM solutions can come with many benefits — from improving user experience and achieving regulatory compliance to reducing IT costs. However, as the threat landscape worsens and digital environments become more complex, companies must ensure their IAM practices can keep up with the demands faced by modern IT systems.
iC Consult covers the whole lifecycle of IAM, breaking up its services into several key areas across the entire IAM value chain to simplify access privileges and help administrators manage applications — no matter where they are hosted.
Identity management and access management
Identity Management and Access Management cover the essential functions of IAM, automatically storing and regulating assigned authorisations to allow employees to access the ever-growing list of resources they need to perform their duties. In a nutshell, these solutions ensure all digital identities (people, groups, devices or applications) are monitored and guarantee the correct access privileges for every user.
Customer IAM
Customer IAM (CIAM) involves collecting and analysing consumer data to provide valuable insights into user behaviour and streamline sign-on experiences. An efficient CIAM system can improve conversion rates, boost customer experience ratings and support GDPR compliance. CIAM regulates customers’ consent to personal data processing — something that organisations must acquire to stay in line with data protection laws.
Identity as a service (IDaaS)
According to iC Consult, IDaaS is the fastest way to manage identities and access privileges in the cloud, digitalising existing processes to enable rapid time-to-market for new business models. By completely outsourcing IAM to an external IDaaS provider, companies can benefit from cloud-based IAM features such as single sign-on (SSO) and multi-factor authentication (MFA) without requiring internal IT teams to set up their own IAM architecture.
Application Programming Interface (API) management
An API is a piece of technology that allows two different programs to communicate with each other; for example, the Met Office provides access to weather data via APIs, which third-party applications then use to update forecasts. With the help of effective API management, companies can publish APIs and gain new data insights to inform decision-making without putting internal systems at risk.
The Internet of Things (IoT)
The IoT — the network of around 13.1 billion devices connected to the internet — is the next big thing in technology. But although the possible applications for the IoT are endless, monitoring security within this rapidly expanding web can be complicated. IoT devices’ APIs must be publicly available but secure to maintain control of potential security vulnerabilities. So, administrators must carefully manage the relationships between different identities and apply all the necessary security protocols.
IT Security
A detailed understanding of general IT security is the cornerstone of any effective IAM model. From data encryption to zero-trust frameworks, system designers must incorporate security considerations at every stage during the development of IAM infrastructures. iC Consult has over 25 years of experience in IAM with certified security, making it well-positioned to integrate IAM services safely.
By tackling some or all these factors in one packaged solution, the IAM consultants at Burning Tree and iC Consult give customers ultimate control over their resources — even as new systems and capabilities are introduced.
Let the experts take IAM off your hands…
Refining IAM strategies is crucial for any business leaders keen to capitalise on the advantages of technological progress. However, as managing infrastructures grows more complex and time-consuming for in-house teams, many opt to alleviate the burden entirely by outsourcing their IAM needs to a provider like iC Consult.
With more than 800 consultants, the iC Consult Group is the leading consultancy, systems integrator and managed services provider for IAM. It specialises in getting involved in all phases of IAM solutions — from planning to implementation operations and managed services — and has successfully delivered more than 4,000 projects worldwide.
So, if your company is looking to outsource its IAM needs to a trusted provider with experience that spans every aspect of modern identity governance, contact us and enquire about iC Consult’s offering today.
All our partners have been carefully selected because we are confident that their products and services are the best in the market. To find out more about Burning Tree’s iC Consult services, please contact info@burningtree.co.uk.