Importance of identity management unveiled at the RSA Conference 2022
Burning Tree recently attended the RSA Conference: an annual event where security professionals partake in an open dialogue about the latest developments in the fast-growing cyber security industry.
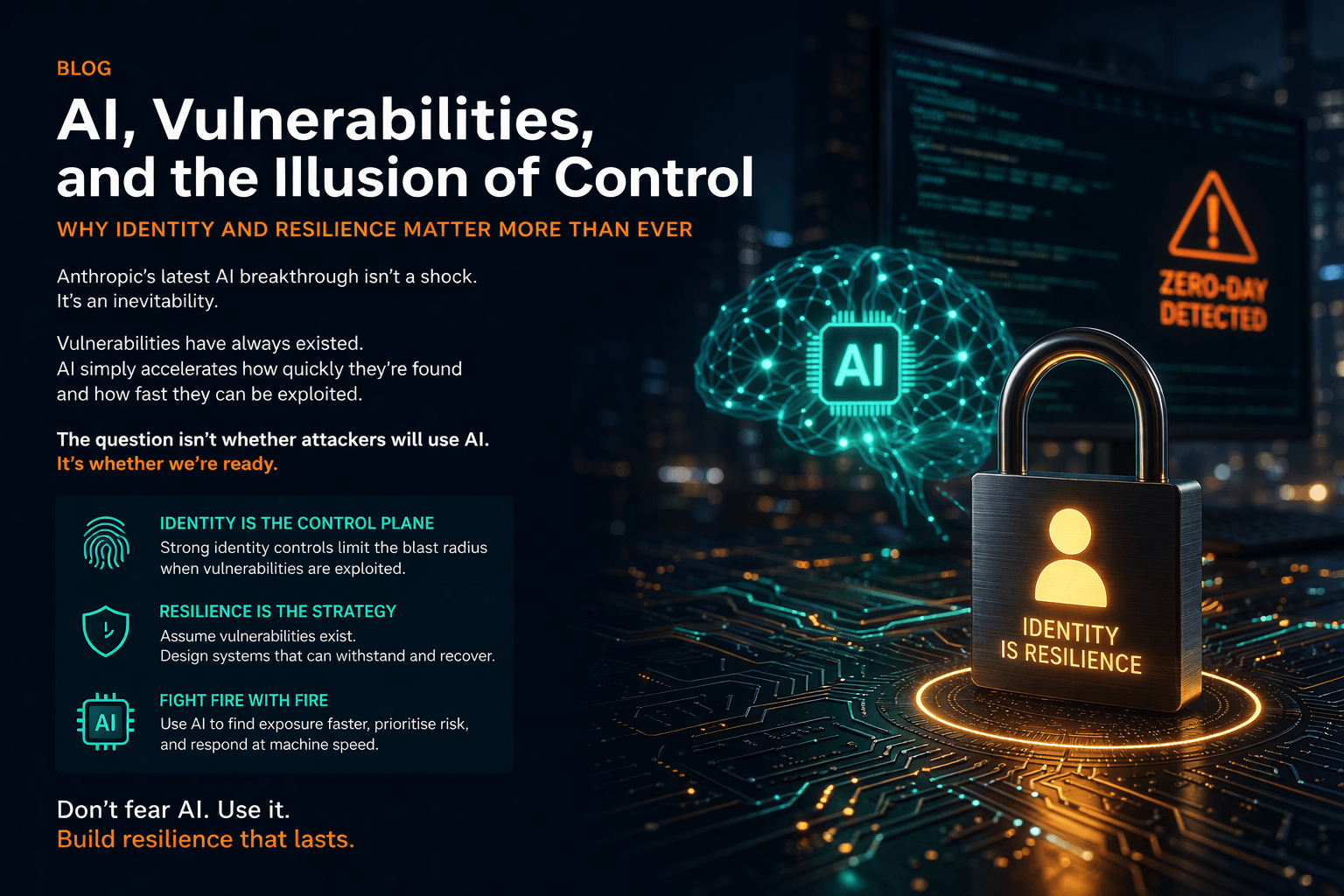
One of the key takeaways from this year’s conference was the value of user identities to security domains. Identity management has remained one of the most pressing challenges for business security since the pandemic, with a large percentage of global organisations experiencing high levels of identity-related attacks.
So, what did we learn about the need for identity security at the RSA Conference — and what should you do to reinforce your cyber defences against the growing threat of an identity-based attack?
The rise in identity-driven cyber security breaches
Identity management involves monitoring and authorising access of the person (or machine) behind the screen and what they can access.
The main priority in identity-based security is keeping the right people in and the wrong people out. Whilst this strategy has always played a part in traditional security measures, such as password-protected account logins and face and fingerprint identification, a need for more robust identity-based security measures has emerged since the onset of COVID-19.
For example, many new opportunities for sophisticated phishing attacks arose in the form of fake COVID-19 vaccination invites and delivery notifications throughout the pandemic. The NHS was forced to warn the public about false Omicron exposure texts several times through the pandemic and most recently in June 2022, evidencing just how persistent these threats are over two years since the pandemic began.
The popularity of hybrid working policies has also been driving increased vulnerability to cyber security attacks during the pandemic, as more employees operate from unprotected Wi-Fi networks whilst working remotely and fail to observe cyber hygiene best practices.
The rising uptake of cloud computing to accommodate remote working comes with a heightened risk of identity-based attacks such as seen through phishing and targeted spear-phishing, which have been some of the most prevalent forms of cyber attack in recent years. Since the government lifted restrictions, more workers also bring compromised devices with weak passwords and a lack of antivirus software into offices, introducing further threats to working environments.
Unfortunately, the longer businesses function without up-to-date cyber security measures, the more time cyber criminals gain to develop more sophisticated and damaging cyber attacks. As a result, companies must consider how they will prevent identity vulnerabilities from impacting their systems and bottom line.
Developing identity-based cyber security strategies
As the actions of sophisticated cyber criminals can be tricky to differentiate from a valid user’s behaviours, attacks driven by user identity are difficult to detect and intercept. However, they are not impossible to prevent.
User-centric cyber security strategies can reduce the risk of cyber security attacks and mitigate the effects of any breaches — all whilst improving user experience.
The following approaches are examples of how our customers effectively manage the threat of identity-driven cyber security threats.
Zero trust
‘Zero trust’ security requires all users to be authenticated, based on the premise that anyone, or anything, could be a cyber security threat. In simple terms, this is a ‘never trust, always verify’ approach designed to ensure every user must demonstrate the validity of their access request, minimising the risk of files, systems and software falling into the wrong hands.
By implementing least-privileged access measures like multi-factor authentication (which involves users passing two or more security checks to access their accounts), businesses can reduce the risk of unauthorised persons accessing sensitive information and launching an attack.
Security endpoints such as desktops, laptops and mobile phones must also employ equally robust authentication methods. Step-up and multi-factor authentication can help strengthen trust, whilst identity as an application programming interface (API) makes for a more reliable system at a reduced risk of fraud.
Customer identity and access management (CIAM)
CIAM is another highly effective security method used to control user access, proven to reduce the risk of security breaches by 75%. Like zero-trust authentication, this method seeks to keep cyber criminals out and verified users in.
A CIAM system harnesses a wide range of security measures to improve cyber security and streamline customer experience simultaneously. For example, single sign-on (SSO) allows users to access multiple applications using just one set of credentials for a more streamlined sign-in experience.
Because CIAM is predominantly motivated by improving customer experience, securing user trust and improving customer retention and outreach, all measures effectively improve cyber security without compromise.
Many businesses are seeking external support from cyber security specialists to seek a CIAM solution that suits the needs of their business. Doing so can help maintain optimum cyber security at all times, with security experts recommending informed measures based on past and present threats.
Identity Governance and Administration (IGA)
IGA is a technology that drives automation into the Joiner, Mover & Leaver (JML) process to support and ensure users in an organisation have the right access at the right time. The process is essential to ensure that conflicts of access, segregation of duties and mandates are enforced, reducing the risk of insider threat.
The multiplying effect of the number of users and the systems they access add to the complication of administration. Without IGA, the task quickly becomes unmanageable. The larger the organisation (more users and many systems), the more complex the process becomes.
IGA programmes can be complex because they impact all prioritised systems and all users. For this reason, it is important to seek assistance from an organisation with experience in delivering IGA and the breadth of knowledge to address organisational change.
To learn more about Burning Tree’s security services and how we could help your business implement appropriate CIAM measures, contact our cyber security specialists at 01252 843014 or email info@burningtree.co.uk.