How can your business put a stop to insider threats?
No business wants to think about the possibility of insider threats within their organisation.
But in 2023, 74% of businesses are vulnerable to this genuine risk — posed by those with access to an organisation's assets.
These insiders could be anyone from negligent current employees, business partners or vendors to disgruntled former staff members who have got their hands on critical and sensitive information within the organisation's network and computer systems.
The consequences of an internal threat can take many different forms, including data breaches, fraud, sabotage of security measures, theft of intellectual property and mistakes.
Unfortunately, most companies only see insider threats once it is too late and irreparable damage has been caused. So, how can you spot incoming threats in time to avoid them?
The danger from within
The first step to identifying insider threats is understanding the two types at play: negligent and malicious.
Negligent insider security threats happen often. Usually, they result from human error, poor judgement, lack of training or falling victim to social engineering tactics such as phishing attacks. This type of insider threat typically falls into either 'the pawn' or 'the goof' category.
Of course, accidents happen. But sometimes, someone in your organisation could have malicious intentions. This kind of insider threat also falls into two categories: 'the collaborator' and 'the lone wolf'.
The pawn
Pawns are employees who are unknowingly manipulated into performing malicious activities. Through accidentally downloading malware or clicking a suspicious link, pawns provide external actors with confidential data that allows the fraudster to wreak havoc with genuine credentials, banking details and other classified information.
For example, in August 2022, several Microsoft employees exposed login credentials to the company's GitHub infrastructure. The information would have given anyone, including attackers, access to Azure servers and other internal Microsoft systems, which could have had devastating effects on the enterprise and its customers.
The goof
Goofs are ignorant users who tend to believe they are exempt from business security policies, actively trying to bypass security controls. Through poor judgement and a lack of training, the goof leaves vulnerable data and resources unsecured — giving attackers free access.
The collaborator
Collaborators work with external actors, such as a company's competitors, to commit a crime. Using their access within the business, the collaborator steals intellectual property and customer information to disrupt business operations (often for financial or personal gain).
The lone wolf
Lone wolves act on their own and are particularly dangerous when they have higher levels of access privilege. An example is a security engineer fired from Facebook after being accused of exploiting his access to privileged information, which he used to stalk women online.
Identify and eliminate
Whilst most organisations are on the lookout for external factors putting their business at risk, they often forget to implement preventative measures to catch out negligent or malicious internal threats.
To keep your business safe from the inside out, here are the actions you must take…
Conduct a risk assessment
Regular risk assessments identify the threats that could affect your company's assets, such as hardware, systems, laptops, customer data and intellectual property, and allow your business to stay on top of evolving risks.
Carrying out security risk assessments also helps to influence the security policies needed to protect your business from the inside. Your security policy should include procedures to identify and prevent malicious activities — specifying who can access the data, under what circumstances, and with whom they can share the information.
Once your policy is in place, clearly communicate to your team why the company is following this policy — and your workforce's role in protecting the company and its assets. Ensure the policy is easy for your team to access and understand and that there is a point of contact should they have any questions.
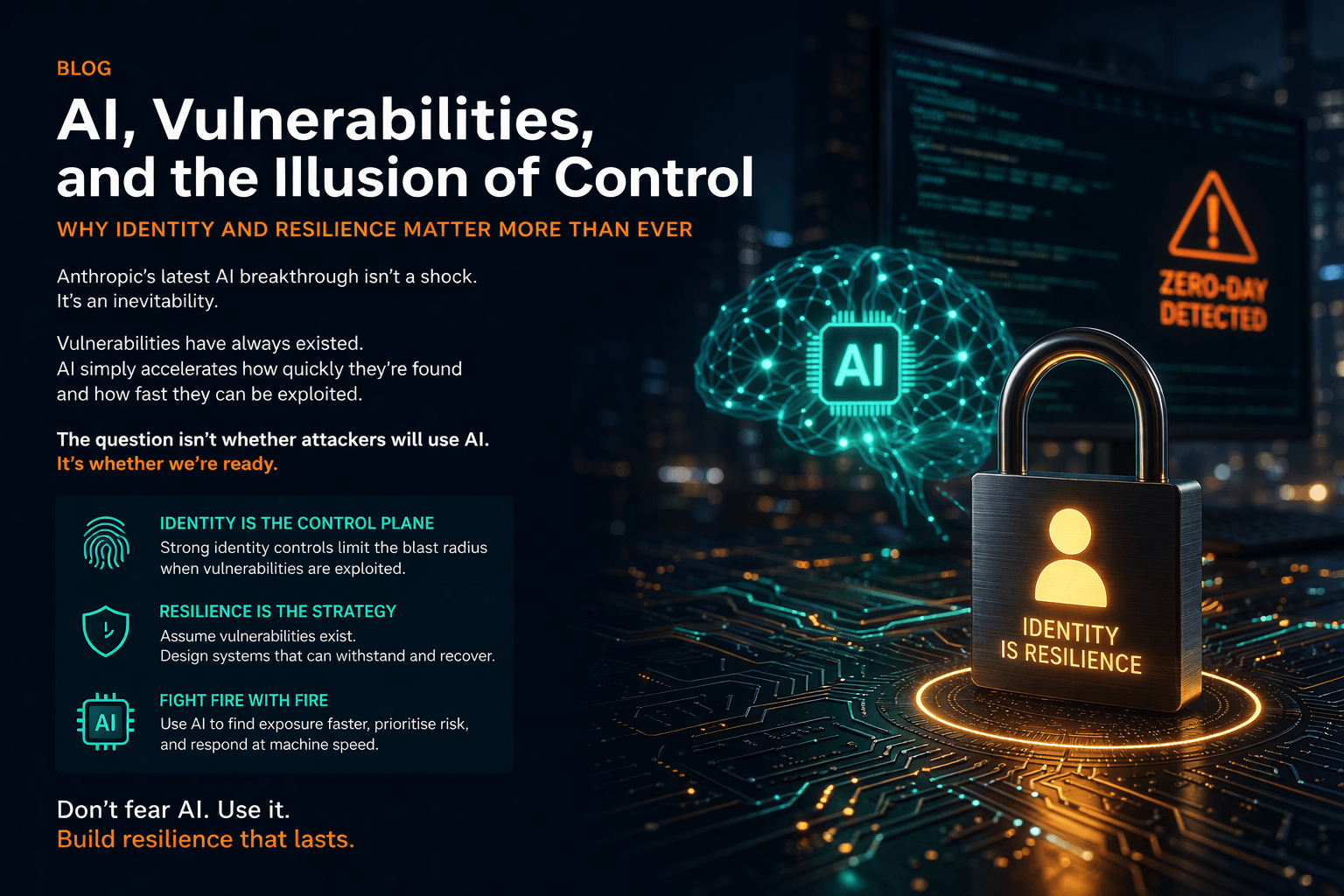
Implement access control
An effective identity and access management (IAM) process helps to identify, authenticate and authorise employees (as well as the hardware and applications they need to access).
With a successful IAM programme in place, you can implement a zero-trust approach and the principle of least privilege — giving you peace of mind that your data, resources and applications are secure and only accessible to those who need them to complete a required task. IAM procedures also allow you to easily offboard employees by removing them from their accounts when they leave the company.
It is especially important to manage the highest risk accounts with Privileged Account Management (PAM) processes and systems. PAM solutions can vault passwords, enforce just in time access and just enough access. They can monitor and even manage sessions as well as control changes and enforce policy in the administration of operating systems and databases.
Perform penetration testing
Often included as part of a security audit, a penetration test is one way a company can gain a true sense of their security defences.
Ideally, this test would use the same techniques as a hacker attempting to breach your systems. These techniques may include simulated attacks like phishing, altering data or installing malware and should be performed annually for optimum coverage of your security measures.
For example, you could conduct a phishing simulation to guard your business against social-engineering threats. This type of simulation aims to train your employees to identify and report fraudulent or suspicious emails — assessing your team's response to find improvement areas.
Once you know where the weak spots are, launch regular security awareness training for your team. Providing training resources like the National Cyber Security Centre's 'Top Tips for Staff' and continuously testing your employee's awareness goes a long way in embedding a culture of security compliance within your organisation.
Introduce 24/7 network monitoring
Every device your employees use to connect to the business network (known as endpoints) represents a potential risk that insider threats can exploit to steal corporate data.
So, each corner of your business should be monitored, including on-premises and cloud environments. Conducting 24/7 monitoring will allow you to identify events requiring an instant response and can increase awareness of your employee's actions.
Endpoint protection platforms should also be installed on your business devices, working in conjunction with 24/7 monitoring, to flag suspicious activity and prevent insider threat actors from downloading malware (either intentionally or accidentally) or using tools to infiltrate your systems.
Reinforce your security systems
By now, most businesses know they need efficient security systems to protect them against cyber threats. But on top of running their organisation, keeping up with the latest safety regulations and updating security software can seem like too many spinning plates.
If that sounds familiar, it may be time to turn to the experts.
Information security specialists can do all the heavy lifting — reviewing your current processes and recommending safer practices based on your particular security needs — to keep your business safe and prevent a breach.
Any business can suffer an attack from an insider threat. Are you concerned about your organisation's security threat risk? Reach out to our team of cyber security specialists and discover how we can help through our consulting services.