7 crucial steps to protect your business from software supply chain attacks
Did you know software supply chain attacks have impacted 62% of organisations? Hardly surprising when, on average, businesses share their data with around 730 vendors…
The stakes are already high for any business that handles highly sensitive and confidential client information online. Throw various third-party suppliers and contractors into the mix, and the risk only increases.
After all, your company is a connected network of vendors, software and people that keep your business operational.
From outsourced services like document reviews and payroll tasks to the use of integral software — your network, applications and sensitive data go through the hands of many third-party providers. And it only takes one to gain unauthorised access, infiltrate your digital infrastructure and deploy malicious code that could bring your business to the ground.
Just ask MGM Resorts International — a major enterprise that came to a halt when the known hackers Scattered Spiders breached their systems and gained control of MGM's IT service management provider Okta and its Microsoft Azure cloud environment. Not only did this jeopardise the applications managed by the IAM platform — but it also put MGM's cloud assets in danger.
Want to avoid a similar fate? Here are seven steps to help you assess the security of your software supply chain and improve your business' risk management approach…
- Uncover your security risks with an assessment
First thing's first: carry out a security assessment. Good security starts at home — and you are the home of your software supply chain.
An assessment will review your software for common security issues, search your business for known breaches and determine whether the systems protecting your networks are securely configured and can detect attacks.
It can be challenging to identify any risks until you have a clear picture of your supply chain. So, you will need a list of your vendors, prioritising their threat level based on how closely they work with your business and what kind of data they handle, how the data flows and where it is stored.
Running an internal security assessment will expose your business' vulnerabilities, making it easier to assess any risks and learn where you need to bolster your cyber security efforts. It is the first stage of a supply chain risk management (SCRM) system, which is essential for any business looking to keep hackers at bay.
However, executing one security assessment will not be enough. The assessment should be re-verified annually (at least).
- Set a precedent for your supply chain
Your firm's security compliance is only as strong as its weakest link.
As such, assessing your existing vendors is vital to confirm they are data-compliant and adhering to regulatory requirements and are certified against a security standard such as ISO 27001. It can also be helpful to know if they are developing at a particular level of CMMI or follow OWASP coding practices.
Certification and coding practices can help to understand if they employ permission and user access controls. Have they educated their staff about cyber awareness? Are they on the ball with penetration testing and network vulnerability tests?
If not, specify what needs to be in place as part of your contract with any third-party providers, clarifying how client data should be handled and the consequences of poor data compliance.
You should also let your vendors know what your business and others in your sector are doing to improve data security, so they can adopt the same rigorous measures — protecting themselves and your clients.
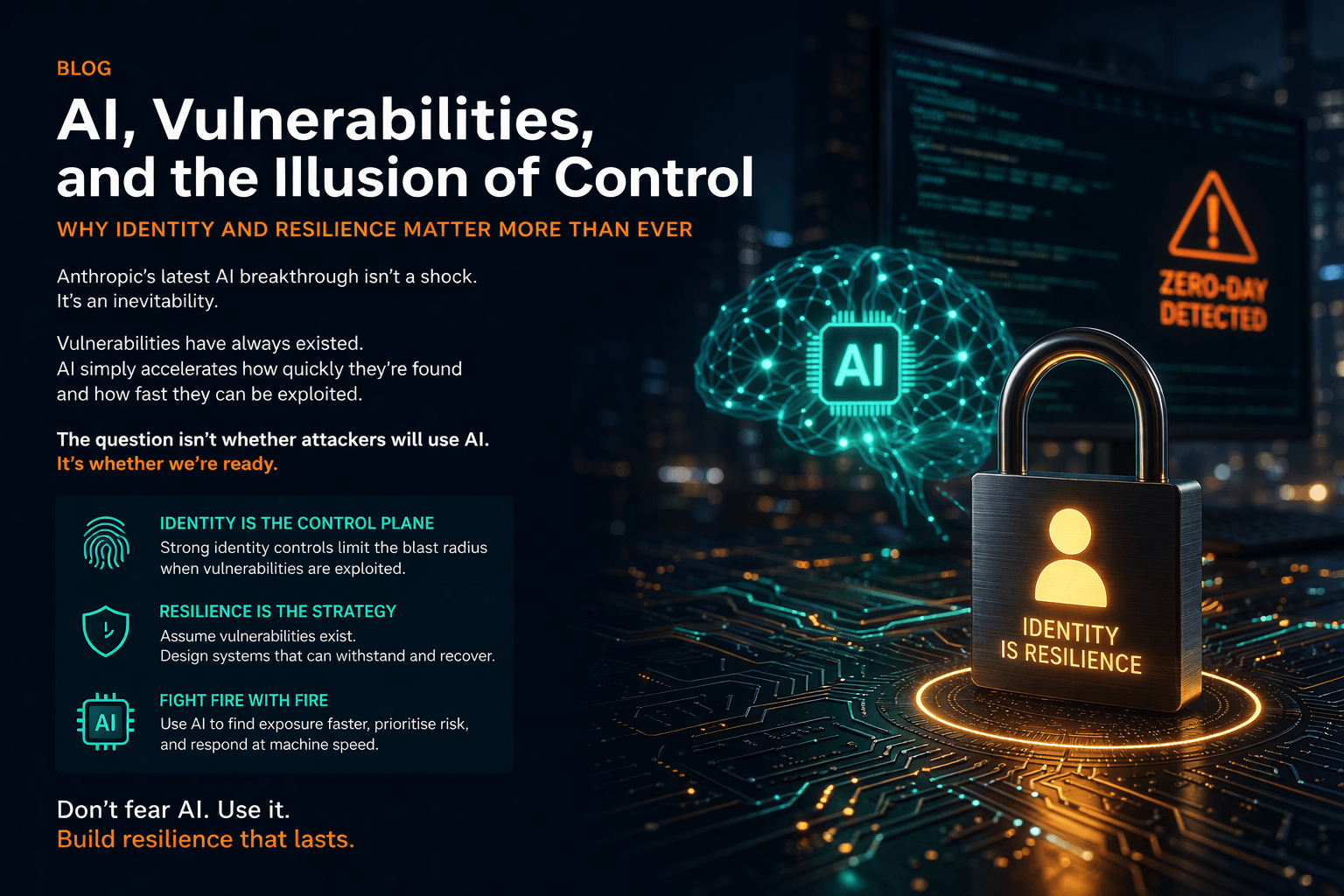
- Establish a zero trust architecture
Rather than assume all authenticated users are trustworthy, the zero trust approach continuously verifies their identity and treats all access requests as if they originate from an unsecured open network.
Every user, device, service or application is connected — and gaining access to private data means first being authenticated with risk-based measures like multi-factor authentication (MFA).
When using MFA, users must pass a few verification tests — for example, by providing a password, one-time passcode and fingerprint or face ID — before being granted privileged access. Essentially, the aim is to make life as difficult as possible for hackers.
- Enforce least privilege access and partition the network
No matter how technically skilled or trustworthy your vendors are, they should only have access to the network resources needed to do their job.
Limiting who can access your critical business systems reduces the risk of accidental or malicious data leaks — either from the users themselves or by sneaky attackers who take over their credentials.
As an added layer of protection, partition the network with microsegmentation, which breaks it into smaller chunks to ensure breaches are contained before they can spread.
By dividing the network, even if one segment becomes compromised, it is less likely to impact the rest of the network.
- Maintain your cyber compliance requirements
The complex nature of modern supply chains has only increased opportunities for cyber criminals to attack any vulnerabilities — and the consequences can be devastating. Not only could your business' reputation be at risk, but in the case of personal data theft, you could incur substantial penalties under the UK's Data Protection Act 2018.
To put yourself in the best position, adhere to the Network and Information Systems (NIS) 2 directive.
The directive requires organisations to understand software supply chain risks, maintain a close relationship with suppliers and regularly update security measures to reduce the risk of cyber attacks originating from third-party sources.
- Insure to ensure cyber safety
If the worst should happen, you want to know you are covered. You would never buy a house without home insurance, so why skip out on your cyber security insurance?
In exchange for a monthly or quarterly fee, your insurance policy transfers some of the financial risks to the insurer and can help cover any losses in the event of a supply chain attack — which could mean the difference between staying in or going out of business.
The catch? Most cyber insurers require a cyber security incident response plan to be in place. On that note…
- Protect your firm from the inside out
Every business should have an effective incident response plan in their back pocket.
Your incident response plan must be documented and easily accessible to your whole team. It should clearly outline each step, from the breach's identification, containment and investigation to risk eradication, system recovery and incident reporting. Be sure to confirm that security incident reporting clauses are also part of your vendors' legal and contractual agreements with your business.
This plan should be reviewed annually to be certain it meets data protection requirements and aligns with your existing SCRM system.
The harsh reality is that most businesses will be impacted by software supply chain attacks at some point. So, with your company's reputation and hordes of sensitive client data on the line, do you really want to wait for disaster to strike before strengthening your supply chain security?
If you are ready to prioritise security improvement for your business, Burning Tree can help. Contact our team of cyber security consultants at 01252 843014 or email info@burningtree.co.uk to discuss our services.