Securing trust across your workforce, partners, and customers
Identity is the foundation of modern cybersecurity. Every user, system, application, and device interaction depends on strong identity and access controls — and when identity fails, organisations fail.
Burning Tree’s Identity & Access Management (IAM) solution helps organisations design, govern, and evolve identity capabilities that are secure, scalable, resilient, and business-enabling. We bring deep, real-world expertise across enterprise IAM, privileged access, and customer identity (CIAM) — aligning security, user experience, and governance.
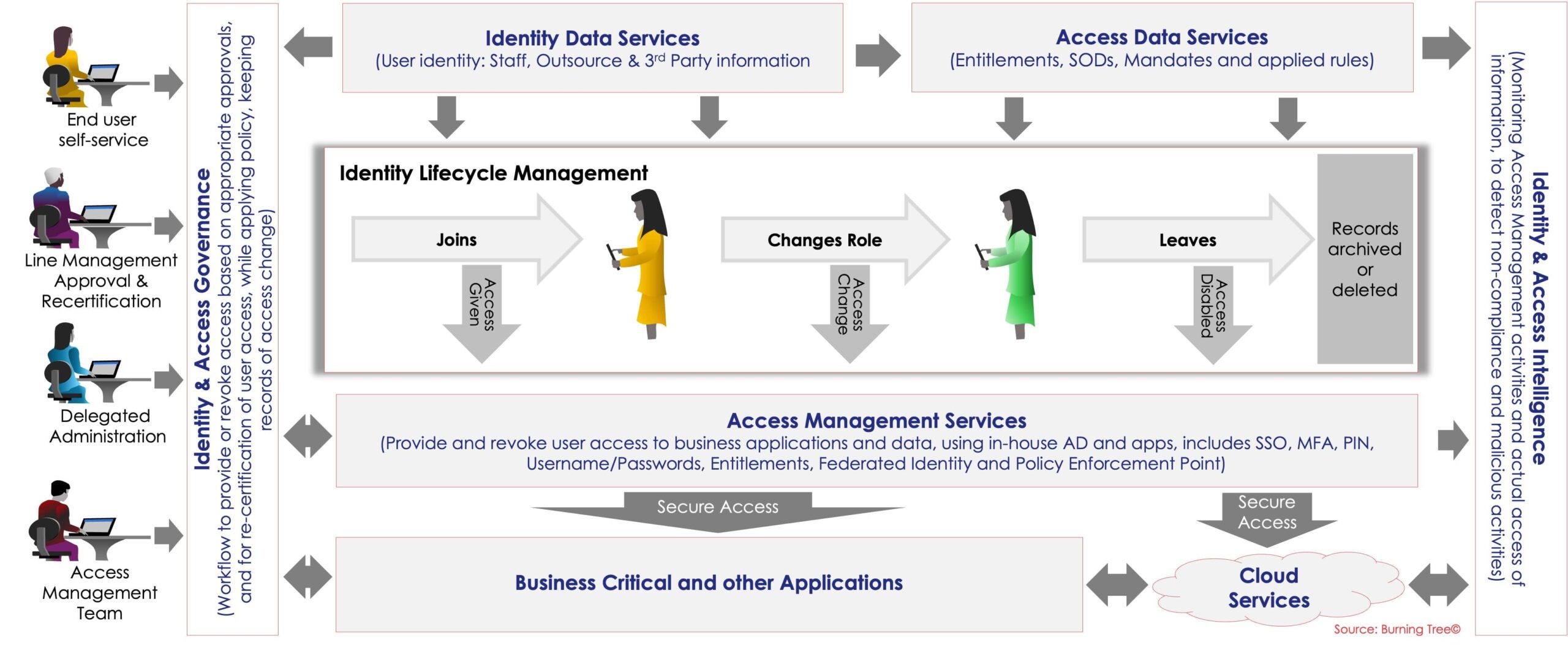
This model illustrates how Identity & Access Management controls and governs access to systems and data across the full identity lifecycle — join, move, and leave. It brings together identity data, access policies, governance, and authentication services to ensure the right people have the right access at the right time. By integrating lifecycle management, approvals, and monitoring, organisations can reduce risk, improve compliance, and enable secure access to business and cloud applications.
Why Identity Matters More Than Ever
Modern environments are dynamic and complex:
- Hybrid and cloud architectures
- Remote and third-party access
- API-driven applications
- Zero Trust adoption
- Regulatory scrutiny
- Growing customer digital channels
Attackers understand this reality — which is why identity is the primary attack vector in most breaches.
IAM is no longer just an IT system. It is a business-critical control that underpins security, compliance, customer trust, and operational resilience.
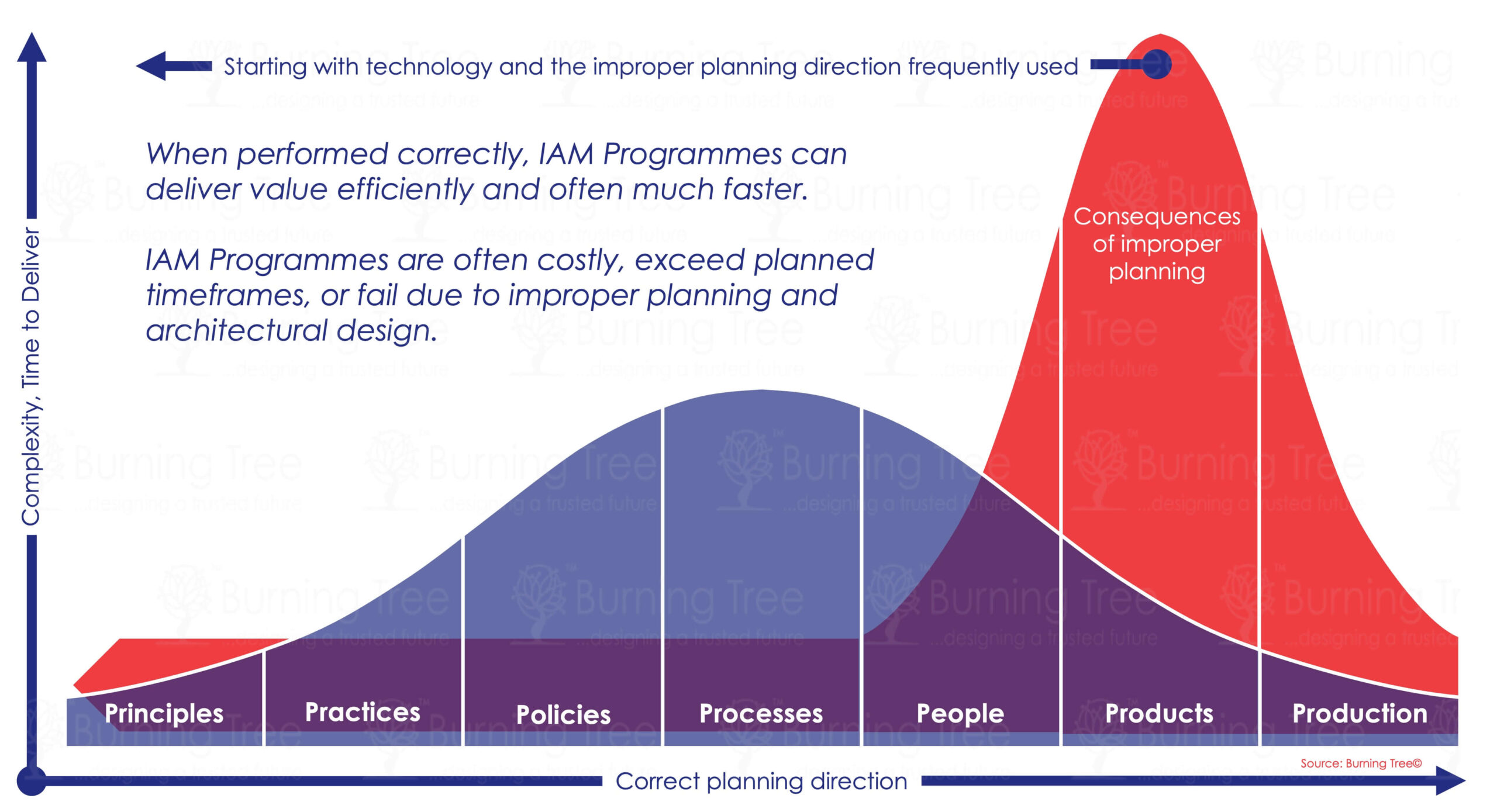
What Makes Burning Tree’s IAM Approach Different
Burning Tree approaches IAM as a strategic capability, not a technology deployment.
We focus on:
- Governance before tools
- Lifecycle and access decisions, not just authentication
- Operating models and accountability
- Integration with Zero Trust, risk, and resilience
- Long-term sustainability and crypto-agility
Our IAM solutions are vendor-neutral, architecture-led, and shaped by decades of hands-on leadership experience.
Business-focused IAM Approach
Enterprise IAM (Workforce & Privileged Access)
Securing access across employees, contractors, partners, and systems
We help organisations design and mature enterprise IAM capabilities that reduce risk while improving efficiency.
Key areas include:
- IAM Strategy & Target Operating Model
- Identity Governance & Administration (IGA)
- Joiner–Mover–Leaver processes, access requests, certifications, and compliance
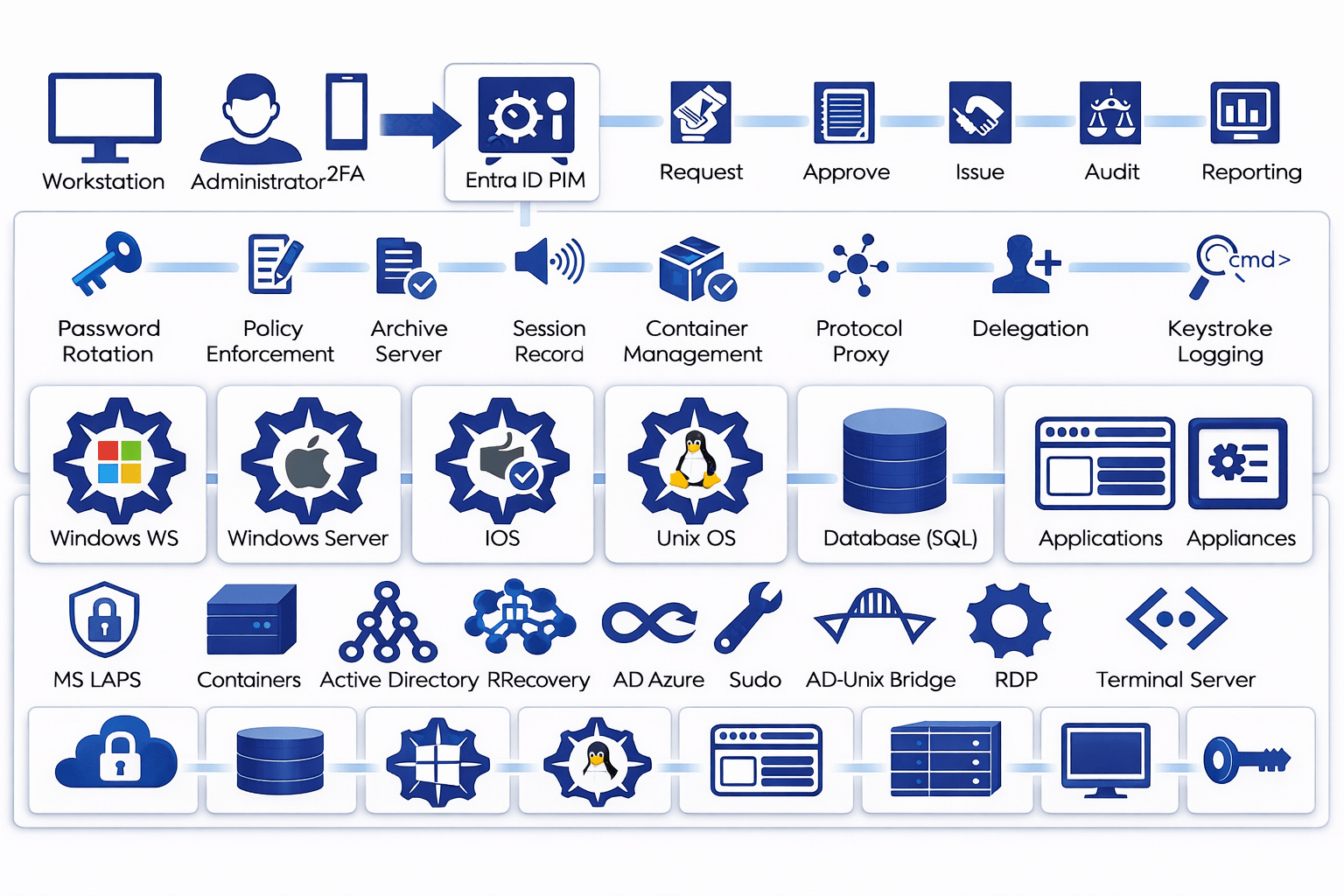
- Privileged Access Management (PAM)
- Vaulting, session control, least privilege, break-glass processes
- Authentication & Federation
- MFA, SSO, passwordless, hybrid and cloud identity
- Access Models
- RBAC, ABAC, and policy-based access decisioning
- Directory & Identity Data Strategy
- IAM Programme Assurance & Recovery
Our focus is on clarity, control, and resilience, ensuring identity supports business operations without becoming a bottleneck.
Privileged Account Management Framework
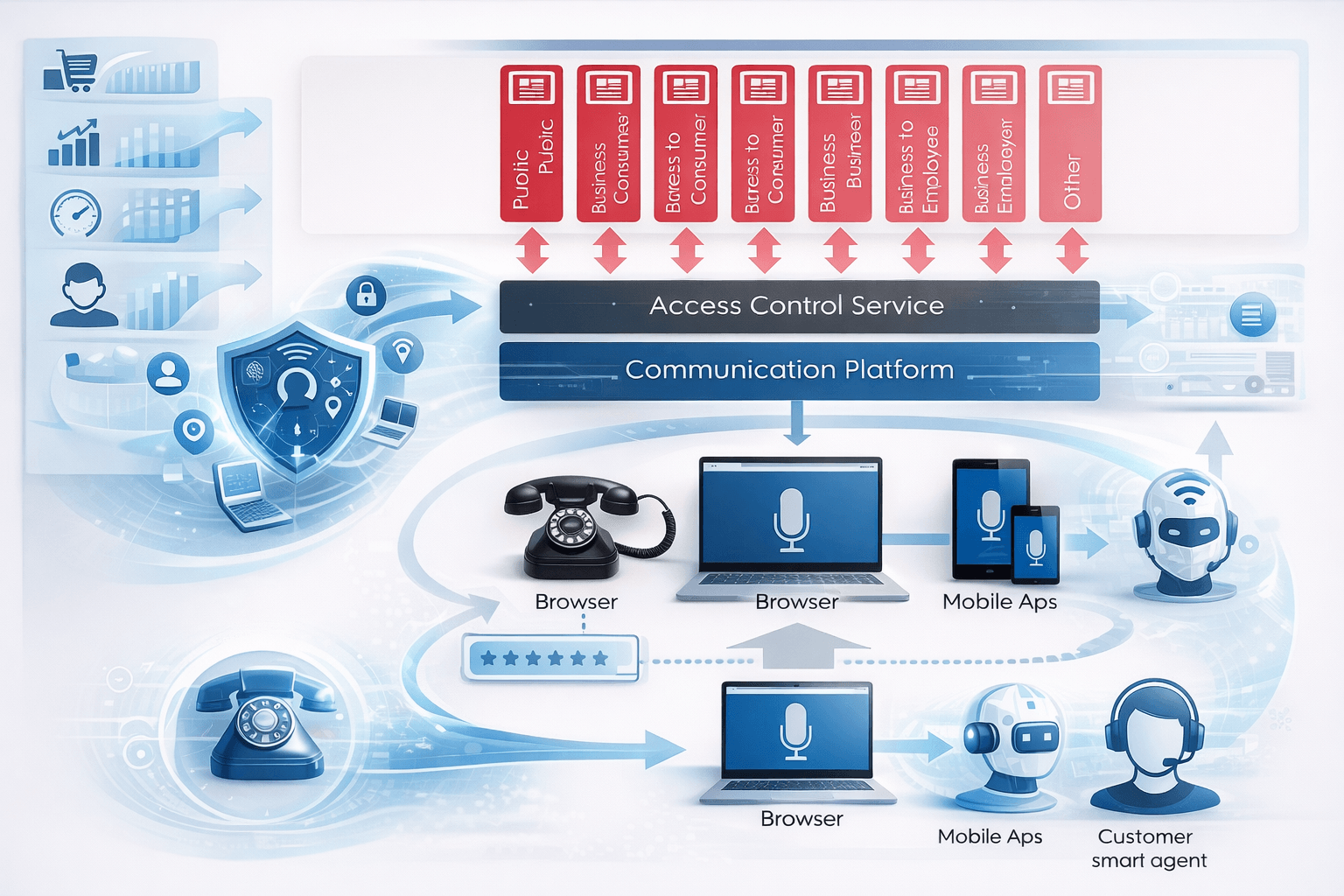
Customer Identity & Access Management (CIAM)
Secure, seamless digital experiences that build trust
Customer identity introduces a different set of challenges — scale, performance, privacy, and user experience — all while maintaining strong security.
Burning Tree helps organisations design CIAM solutions that protect customers and data while enabling growth.
Key areas include:
- CIAM Strategy & Architecture
- Secure Registration, Authentication & MFA
- Consent, Privacy & Data Protection Alignment
- Identity Federation & Social Login Integration
- API-Driven Identity Services
- Fraud Reduction & Identity Risk Controls
- Resilience, Availability & Scalability Design
We ensure CIAM solutions balance security, compliance, and customer experience — without compromise.
Innovating with Customer Experience