The Achilles’ Heel of Modern Business: Ransomware and the Fall of Big Brand Companies
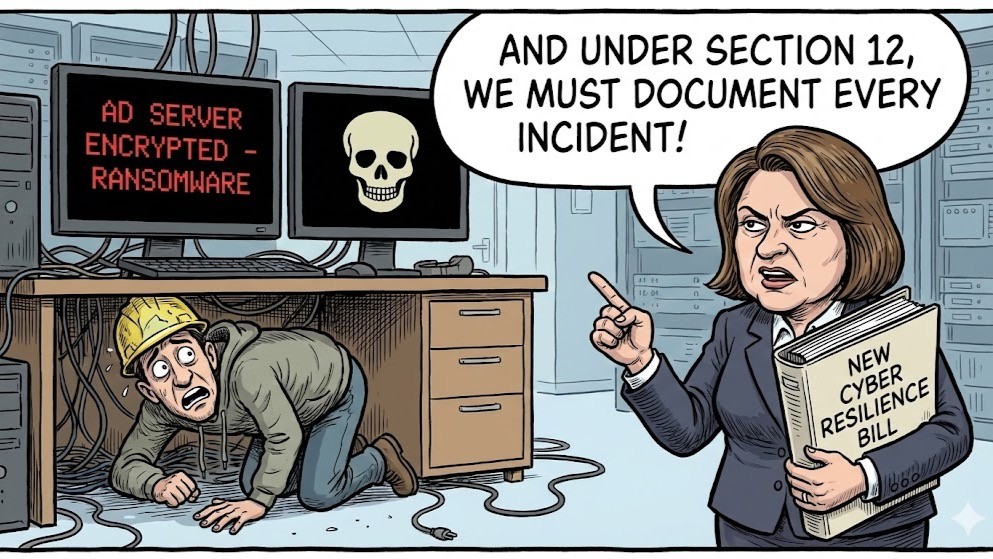
The recent cyber-attacks on well-known retail organisations such as Harrods, M&S, The Co-operative Group, Tesco, and other sectors are a stark reminder of an escalating cyber threat landscape. Threat actors are shifting their focus, increasingly targeting critical infrastructure systems that may not be customer-facing but are utterly essential to business operations.
Among the most devastating targets is Active Directory (AD). When AD is compromised or taken down, the ripple effects are immediate and severe. User authentication fails, applications break, access to systems is lost, and operations grind to a halt. Recovery is complex, time-consuming, and costly.
The Hidden Risk: Underinvestment in Critical Infrastructure Security
Despite their vital role, Active Directory and other back-end infrastructure components are often deprioritised in security investment. They’re not revenue-generating, they’re invisible to the customer, and in many organisations, they’re still managed with legacy mindsets and tools. That needs to change urgently.
At Burning Tree, we specialise in helping organisations secure and future-proof their critical infrastructure. Here are seven key recommendations to strengthen your defences and enhance your ability to respond and recover:
1. Account Discovery and Cleanup
Over time, user and service accounts proliferate—many dormant, misconfigured, or with excessive privileges. These become low-hanging fruit for attackers.
- Conduct a complete inventory of AD accounts.
- Identify unused or orphaned accounts and remove or disable them.
- Enforce least privilege principles for active accounts.
2. Harden Active Directory: Lock Down Changes, Access and Governance
Misconfigurations or open permissions are a common entry point for lateral movement.
- Implement strict change management policies.
- Segregate duties and apply role-based access controls (RBAC).
- Use Group Policy and configuration baselines to enforce secure settings.
3. Monitor for Unauthorised Changes or Installations
Early detection is key. Ransomware campaigns often leave signs, such as unauthorised account creations, privilege escalation, and rogue installations.
- Deploy real-time monitoring and alerting tools.
- Track changes to critical AD objects and configurations.
- Correlate suspicious activity with known attack behaviours.
4. Protect High-Value Accounts with Privileged Access Management (PAM)
Domain Admins and other high-privilege accounts are prime targets. If compromised, they give attackers the keys to the kingdom.
- Remove standing privileges wherever possible.
- Implement just-in-time access for admin accounts.
- Use PAM tools to manage, audit, and expire privileged sessions.
5. Prepare for the Worst: Use AD Recovery Solutions
When AD goes down, every minute counts; manual recovery from ransomware can take days if it’s even possible.
- Use AD recovery tools that offer clean, verified restoration.
- Regularly back up AD and test those backups.
- Ensure separation of backup and production environments.
6. Training and Awareness
Technology alone is not enough. Human error, be it a phishing click or poor password hygiene, remains a leading cause of breaches.
- Deliver ongoing cyber awareness training.
- Include specific training for IT and security teams on AD protection.
- Simulate real-world attacks to reinforce learning.
7. Run Tabletop Exercises and Recovery Tests
You don’t want the first time you test your recovery to be during a live incident.
- Run regular tabletop exercises with IT, security, and executive teams.
- Include ransomware scenarios specifically targeting AD.
- Continuously refine incident response and recovery playbooks.
Technology Enables, Process Sustains
Proven technologies, whether native to Microsoft or through third-party platforms, can support all of the capabilities outlined above. However, even the best tools will fail under pressure without mature processes and a strong governance framework.
Robust cybersecurity isn’t just about technology—it’s also about process. Day-to-day procedures like helpdesk authentication, password resets, and account re-enabling are frequent targets for attackers looking to exploit human or procedural weaknesses. If these processes lack proper verification steps, logging, or oversight, they can quickly become the weakest link in your security chain. It’s essential to regularly review and test these operational workflows to ensure they are resilient, auditable, and aligned with your broader security strategy.
Cyber resilience is not just about defence; it’s about recovery. At Burning Tree, we assist our clients in building secure foundations, reducing risk, and be ready when, not if, something goes wrong.
Let’s talk if you’re concerned about your AD security posture or want to test how resilient your organisation really is.