Security Governance & Strategy
Security Governance & Strategy
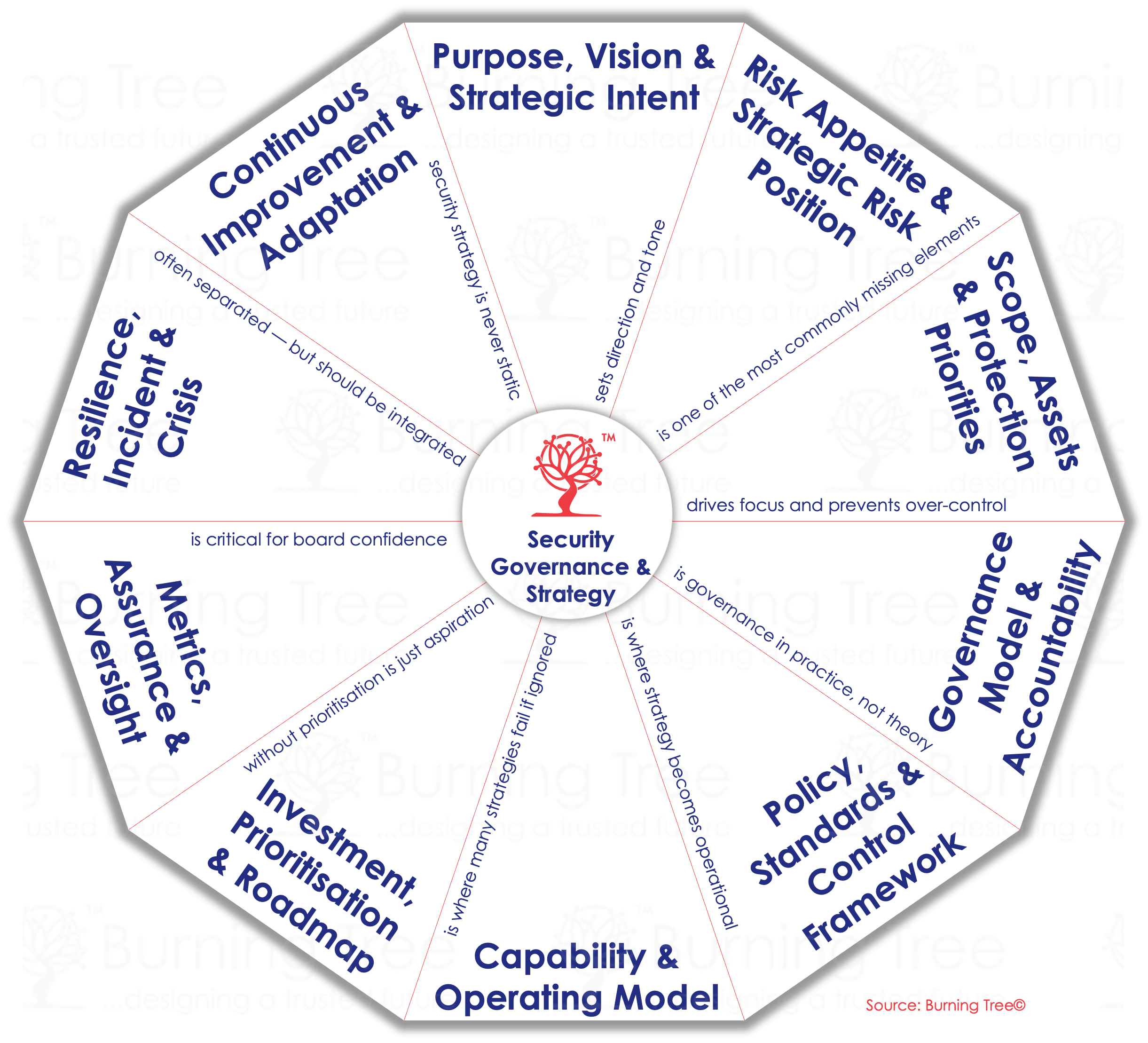
Cybersecurity Strategy Development
Define an enterprise-wide cybersecurity strategy aligned to business goals, risk appetite, and regulatory obligations. Includes vision, principles, and multi-year roadmap. The diagram below represents our framework for delivering a cybersecurity strategy.
Cyber Governance Framework Design
Develop governance models, policies, standards, and procedures aligned to NIST, ISO 27001, CIS, and CCM.
Cyber Operating Model & Target State Design
Design the people, process, and technology structure required for effective security management, including roles, RACI, decision rights, and governance boards.
CISO Advisory & Fractional Leadership
Provide board-level guidance, strategic advisory, and interim leadership during transitions or transformation programmes.
Cyber Metrics, KPIs & Management Reporting
Define security KPIs, risk dashboards, performance indicators, and executive reporting models.
Control Framework Mapping & Rationalisation
Map multiple standards (NIST/ISO/CIS/CCM) into a unified control set to simplify compliance and reduce duplication.
Cybersecuity Governance
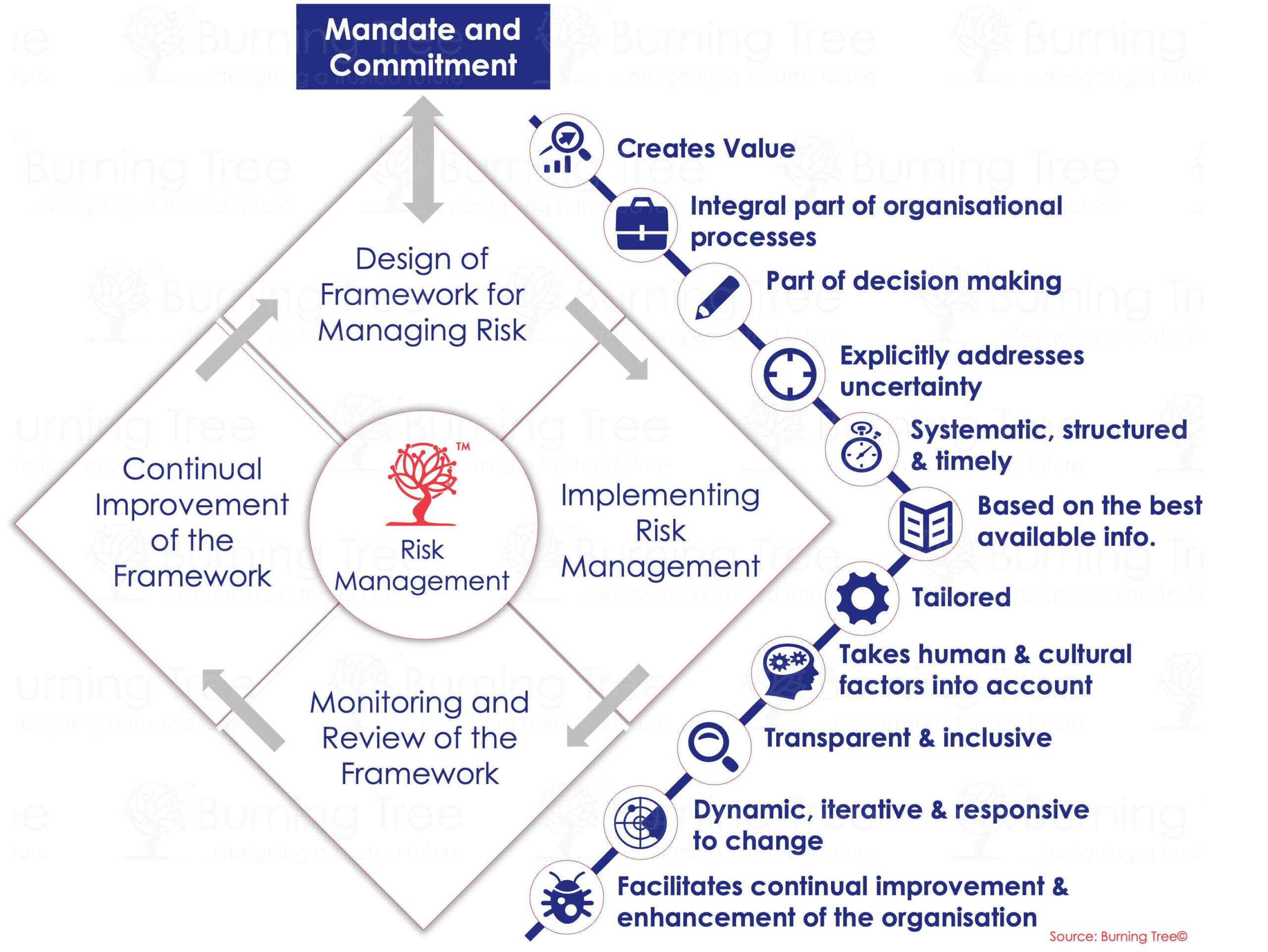
Risk Management
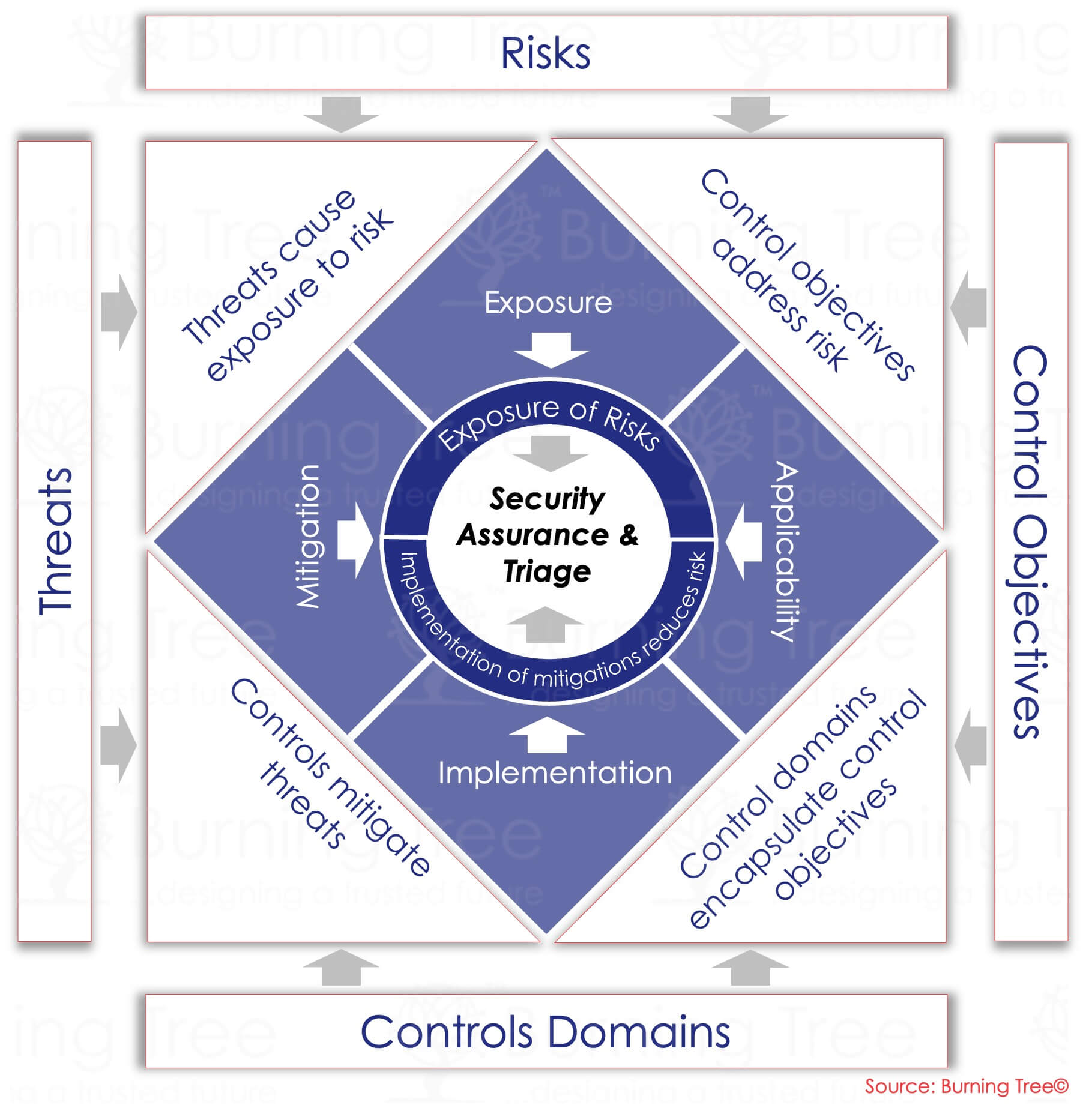
Enterprise Cyber Risk Assessment
Perform end-to-end cyber risk assessments covering assets, threats, vulnerabilities, controls, and treatment plans.
Risk Appetite & Policy Definition
Define the risk appetite statement, tolerances, exception process, and escalation pathways.
Threat Modelling & Scenario Analysis
Use STRIDE, MITRE ATT&CK, and adversary techniques to identify attack paths and prioritise defences.
Third-Party & Supply Chain Risk Assessment
Evaluate vendors, SaaS platforms, cloud services, and outsourced partners for assurance and compliance.
Cyber Risk Quantification (CRQ)
Translate cyber risk into financial impact to support prioritisation, insurance decisions, and board reporting.
Assurance & Compliance
Cybersecurity Controls Assessment
Independent review of controls aligned to NIST, ISO, CIS, CCM, FCA/PRA, or custom frameworks.
CMMI Security Maturity Assessment
Evaluate organisational capabilities against the CMMI cybersecurity model, with detailed benchmarking.
Policy & Standards Compliance Review
Assess compliance against corporate policies, regulatory standards, or industry frameworks.
Third-Party Security Assurance
Evaluate suppliers and partners through questionnaires, attestations, and on-site assessments.
Programme & Project Assurance
Independent oversight of major cybersecurity or transformation initiatives.