Designing secure architectures that protect platforms, data, and applications at scale.
Security Architecture & Design
Enterprise Security Architecture
Define principles, patterns, reference architectures, and guardrails for secure design across the organisation.
Cloud Security Architecture (AWS/Azure/GCP)
Design secure cloud landing zones, network models, identity boundaries, controls, and governance frameworks.
Application & API Security Architecture
Perform architectural reviews for apps and APIs, including authentication, authorisation, encryption, and secure coding alignment.
Data Security Architecture
Develop data classification models, encryption frameworks, DLP strategy, and access governance patterns.
OT/ICS Security Architecture (Optional)
Define secure architectures for industrial environments and SCADA systems.
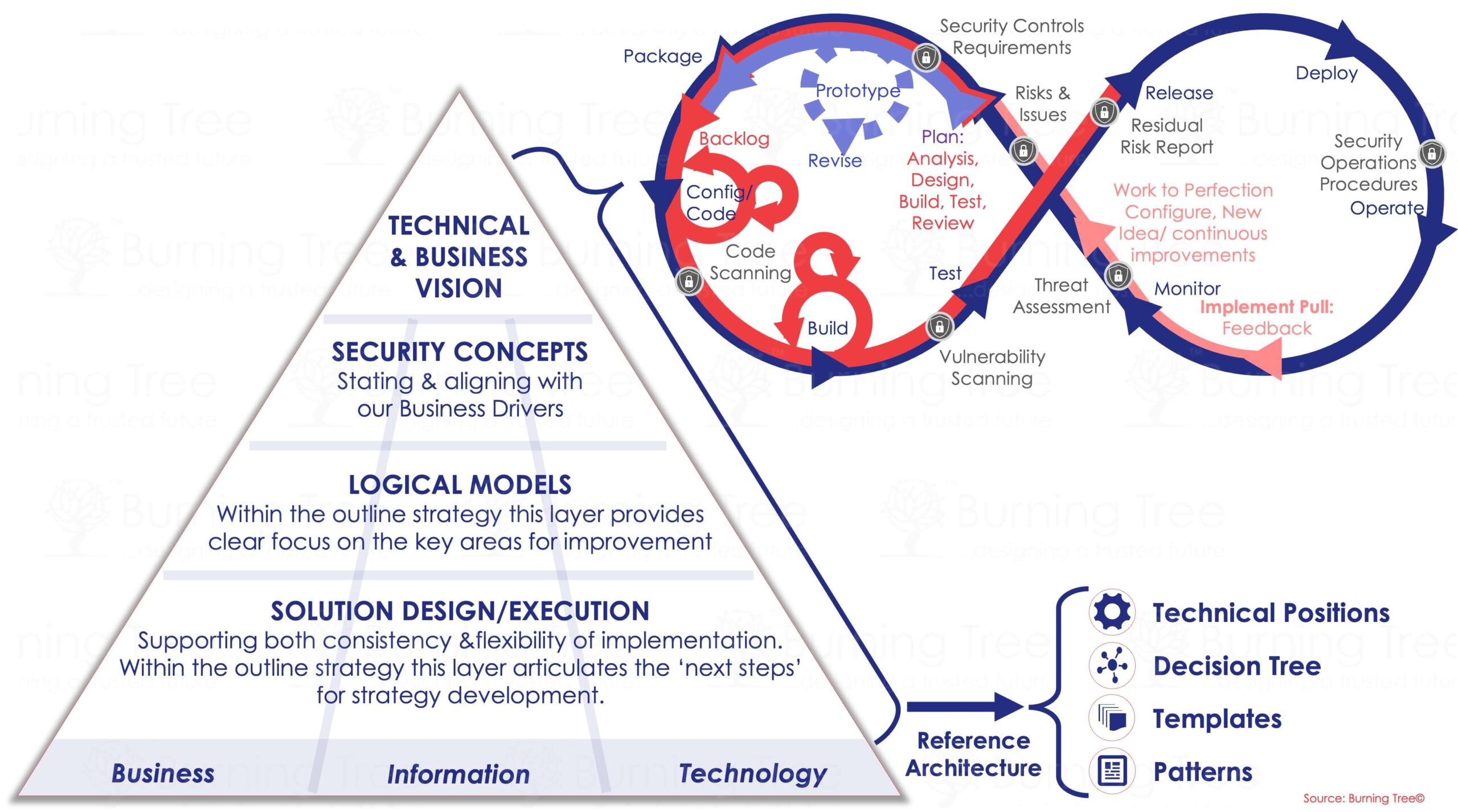
Burning Tree Framework
Design the people, process, and technology structure required for effective security management, including roles, RACI, decision rights, and governance boards.
Network & Infrastructure Security
Network Security Assessment
Review network design, segmentation, firewalling, access controls, and monitoring controls.
Secure Network Design & Segmentation
Design segmented, micro-segmented, or Zero Trust-aligned network architectures.
Endpoint & Server Security
Define endpoint protection, EDR/XDR strategy, configuration standards, and patching governance.
Secure Remote Access Strategy
Design secure VPN, ZTNA, and remote working architectures.
Data Protection & Information Security
Information Classification & Handling Framework
Develop classification schema, handling rules, and governance structures.
DLP Assessment & Strategy
Assess DLP coverage and define a strategy for endpoints, cloud, email, and data flows.
Encryption & Key Management Strategy
Define encryption practices for data in transit, at rest, and key lifecycle governance.
Data Governance Operating Model
Define roles, processes, and stewardship for enterprise data security and privacy.
Cloud Security
Cloud Security Assessment (CIS & CCM aligned)
Evaluate cloud posture, configuration, identity boundaries, monitoring, and governance.
Cloud Governance & Landing Zone Design
Define cloud operating model, segmentation, control sets, and automation guardrails.
Container & Kubernetes Security
Assess cluster configuration, networking, access control, and workload security.
SaaS Security Assurance
Review SaaS platforms for identity, access, configuration, compliance, and integration risks.
Application Security & DevSecOps
Secure SDLC Design
Embed security controls into each phase of the development lifecycle.
Application Security Assessment
Review application architecture, configuration, identity, data flows, and vulnerability posture.
API Security Assessment
Evaluate authentication, authorisation, rate limiting, logging, and encryption for APIs.
DevSecOps Framework & Tooling Strategy
Define pipeline security, scanning strategy (SAST/DAST/SCA), and automated controls.
