Ransomware is Crippling our Companies — It’s Time to Prioritise What Really Matters.
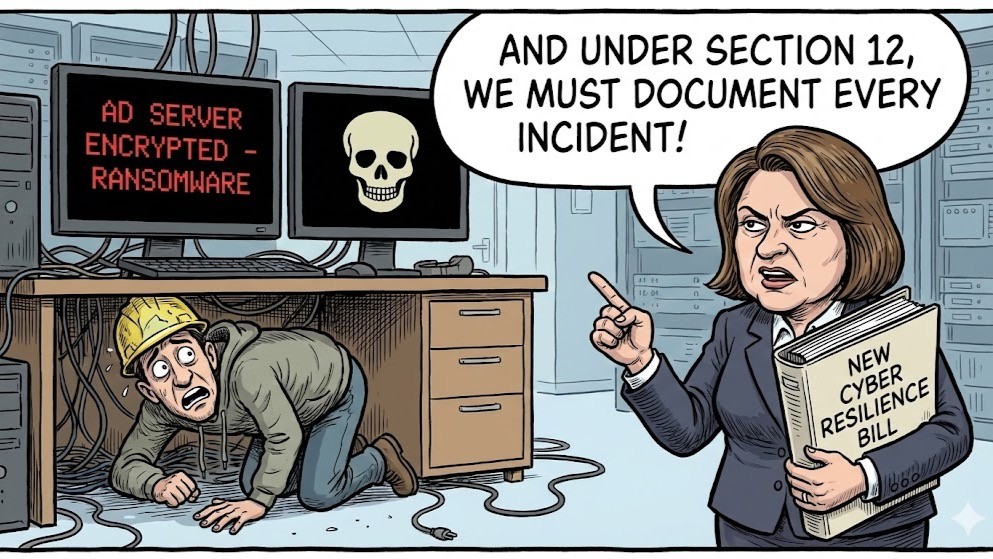
The recent cyber-attacks on well-known retail organisations such as Harrods, M&S, The Co-operative Group, Tesco, and other sectors are a stark reminder of an escalating cyber threat landscape. Some of these breaches, attributed to the hacking group Scattered Spider, were not the result of sophisticated technical exploits but rather the manipulation of basic operational processes. WSJ – Hacking Group That Wreaked Havoc on Las Vegas Appears to Be Back
Scattered Spider, a group known for its social engineering tactics, exploited weaknesses in helpdesk procedures, convincing IT staff to reset passwords and grant access to privileged accounts. This method of attack underscores a glaring issue: the lack of robust, verifiable processes in handling routine IT tasks. The Times – M&S and Co-op cyberattackers ‘tricked IT into resetting passwords’
Kieran Wadforth’s analysis reveals that Scattered Spider has evolved tactics, employing tools like the DragonForce ransomware and Spectre RAT v2.0 to infiltrate and disrupt systems. Their operations are characterised by a deep understanding of corporate IT workflows and an ability to adapt quickly, making them a formidable threat. Silent Push – Scattered Spider: Still Hunting for Victims in 2025
So, what should organisations be asking themselves?
- Are our helpdesk procedures equipped to verify identities beyond basic questioning?
- Do we have stringent protocols for password changes and account re-enabling?
- How regularly are these processes reviewed and tested against social engineering tactics?
- What happens if a hacker calls a company employee and claims to be from the Company Helpdesk? What information would that employee disclose?
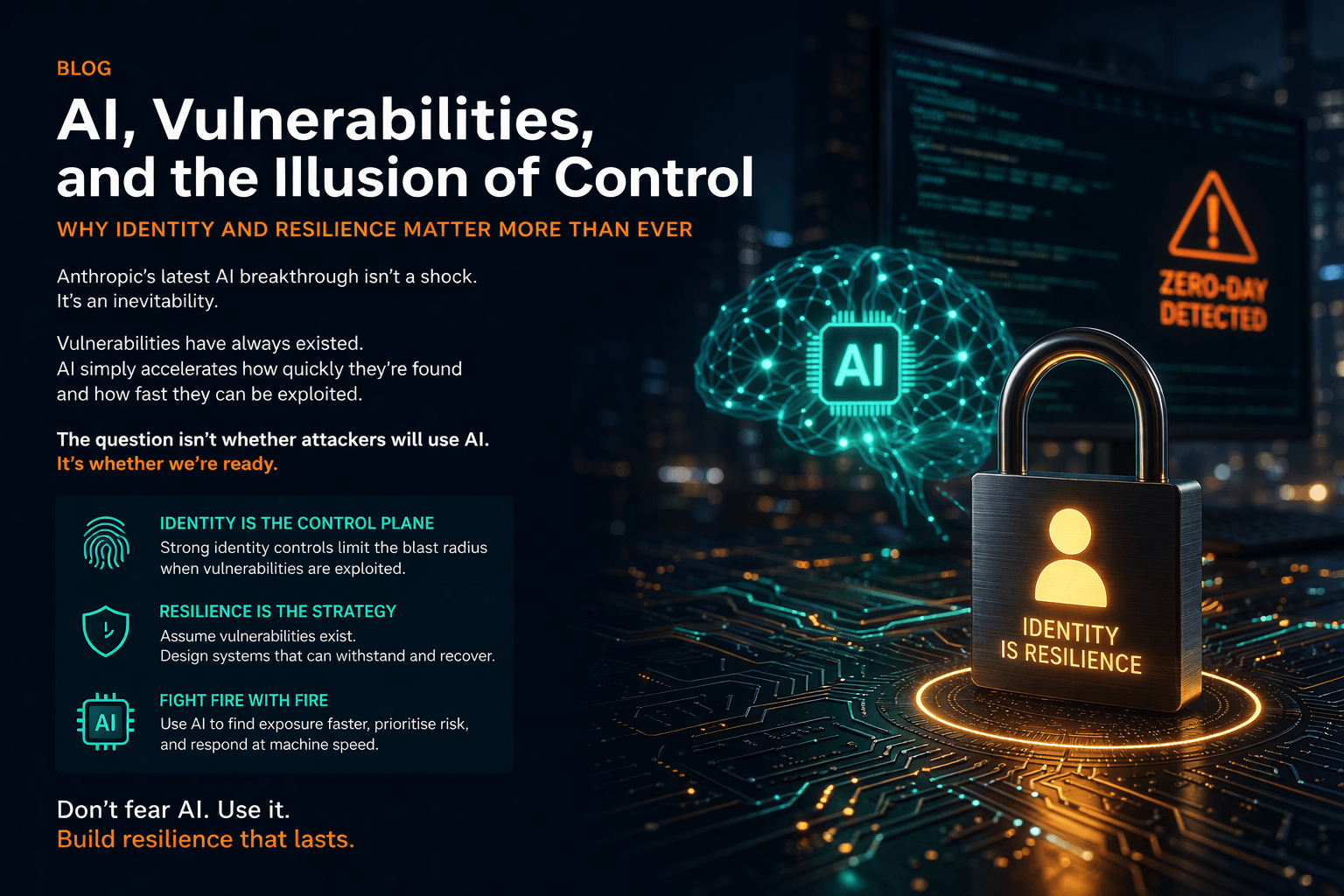
Technology alone isn’t the panacea for cybersecurity threats. Without fortified processes and a culture of vigilance, organisations remain susceptible to attacks that exploit human and procedural weaknesses.
Robust cybersecurity isn’t just about technology—it’s also about process. Day-to-day procedures like helpdesk authentication, password resets, and account re-enabling are frequent targets for attackers looking to exploit human or procedural weaknesses. If these processes lack proper verification steps, logging, or oversight, they can quickly become the weakest link in your security chain. It’s essential to regularly review and test these operational workflows to ensure they are resilient, auditable, and aligned with your broader security strategy.
In conclusion, it’s imperative for businesses to shift their focus from solely investing in advanced technologies to also strengthening their internal processes. By doing so, they can build a more resilient infrastructure capable of withstanding the evolving tactics of cyber adversaries like Scattered Spider.
Cyber resilience is not just about technology. It’s about process. At Burning Tree, we help our clients build secure foundations, reduce risk, and be ready when, not if, something goes wrong.
Let’s talk if you’re concerned about your cybersecurity posture or want to test your organisation’s resilience.