Turning strategy into sustainable cybersecurity capability
Security transformation isn’t about purchasing new tools or merely meeting compliance targets. It’s about developing coherent, resilient capabilities that defend the organisation, support the business, and adapt as risks evolve.
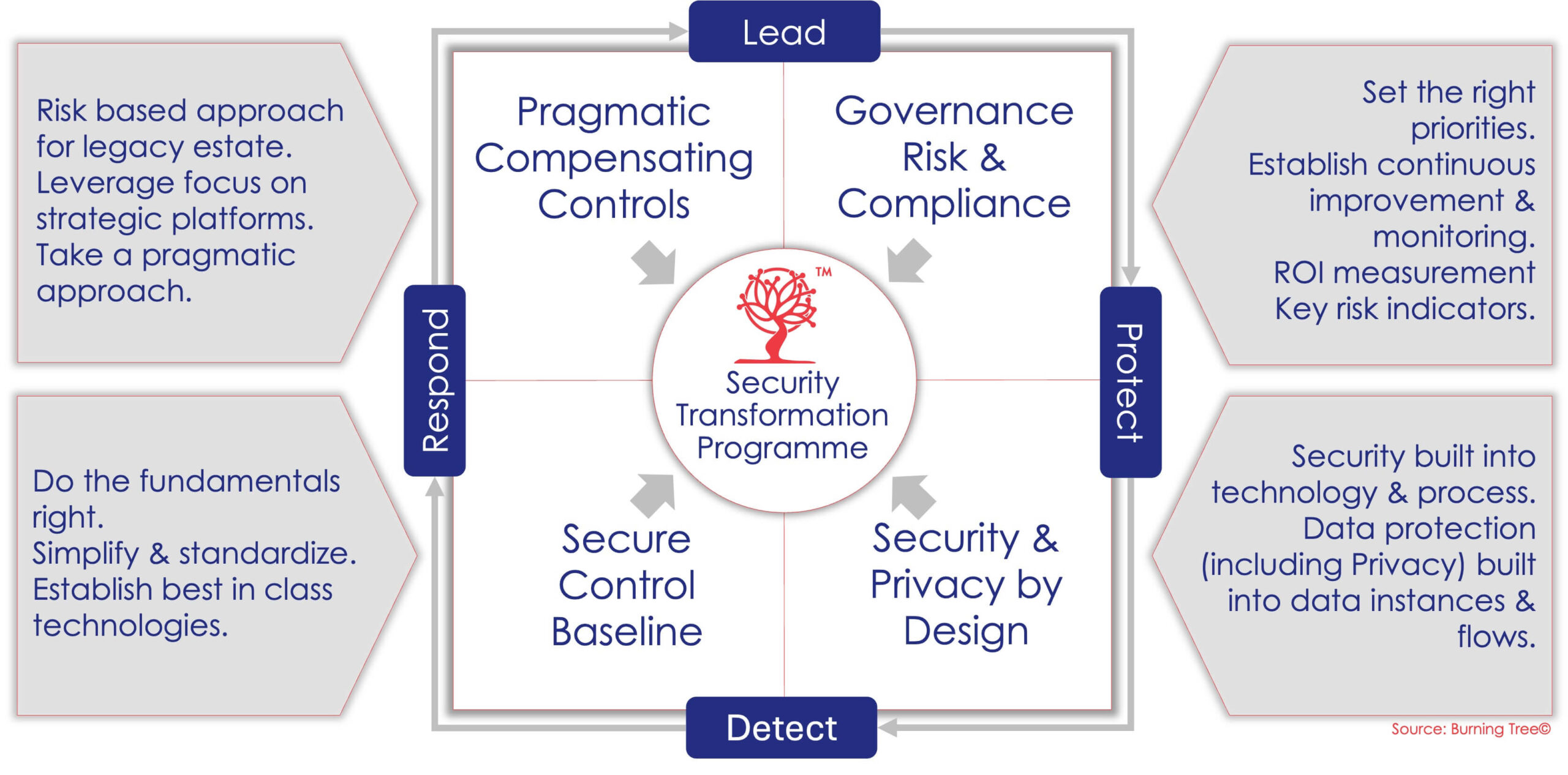
Burning Tree’s Security Transformation solution helps organisations shift from fragmented, reactive security to a mature, integrated, and business-aligned security capability. We guide leaders through change that is practical, proportionate, and built to endure.
Why Security Transformation Fails
Many security transformation programmes struggle because they:
- Focus on technology before governance and operating model
- Address symptoms rather than root causes
- Lack executive sponsorship or clear accountability
- Are driven by compliance instead of risk and resilience
- Overlook people, culture, and ways of working
Burning Tree addresses these challenges by putting leadership, clarity, and purpose at the centre of transformation.
What Makes Burning Tree’s Approach Different
We approach security transformation as a business change programme, not an IT initiative.
Our approach is:
- Strategy-led — aligned to business objectives and risk appetite
- Identity-centric — recognising identity as the foundation of modern security
- Framework-aligned — grounded in NIST, ISO, CIS, CCM and CMMI maturity models
- People-focused — addressing skills, culture, and accountability
- Outcome-driven — focused on measurable improvement, not activity
Transformation is guided by experienced security leaders who have delivered change under real-world constraints.
What We Transform
Our Security Transformation solution spans the full cybersecurity landscape, including:
- Governance & Leadership
Strategy, policies, accountability, funding, and executive oversight. - Risk Management
Risk identification, prioritisation, treatment, and integration with enterprise risk. - Identity & Access Management
Workforce IAM, PAM, CIAM, and Zero Trust identity foundations. - Security Architecture & Controls
Network, cloud, data, application, and Zero Trust-aligned security architecture. - Security Operations & Resilience
Detection, response, incident management, and recovery capability. - Third-Party & Supply Chain Security
Vendor assurance, dependency management, and operational resilience. - Culture & Capability
Skills, behaviours, training, and ways of working.
How the Transformation Works
Burning Tree delivers security transformation through a structured, phased approach:
- Understand & Diagnose
Using our 360° Assessment & Benchmarking model, we establish a clear baseline of maturity, risk, and capability. - Define the Target State
We define what “good” looks like for your organisation — balancing ambition, risk tolerance, and practicality. - Build the Roadmap
We create a prioritised, multi-phase roadmap that aligns security improvements with business change. - Enable Delivery
We provide leadership, assurance, and hands-on support to guide implementation and decision-making. - Embed & Sustain
We help embed governance, metrics, and ownership so improvements endure beyond the programme.
What You Receive
Security Transformation engagements typically deliver:
- Clear security vision and strategy
- Defined target operating model
- Prioritised transformation roadmap
- Architecture and control guidance
- Governance, metrics, and reporting models
- Programme assurance and leadership support
- Improved maturity, resilience, and confidence
Why Burning Tree Is Trusted
Burning Tree is trusted because:
- We have led transformation, not just advised on it
- We understand regulatory and operational realities
- We communicate clearly with boards and executives
- We are independent and vendor-neutral
- We lead with integrity and long-term stewardship
Our success is measured not by how much we change — but by how confident and capable you become.
