Preparing today for tomorrow’s cryptographic reality
Quantum computing will fundamentally change the security assumptions that underpin today’s digital world. While large-scale, fault-tolerant quantum computers are not yet mainstream, the risk is already present: encrypted data can be captured today and decrypted in the future.
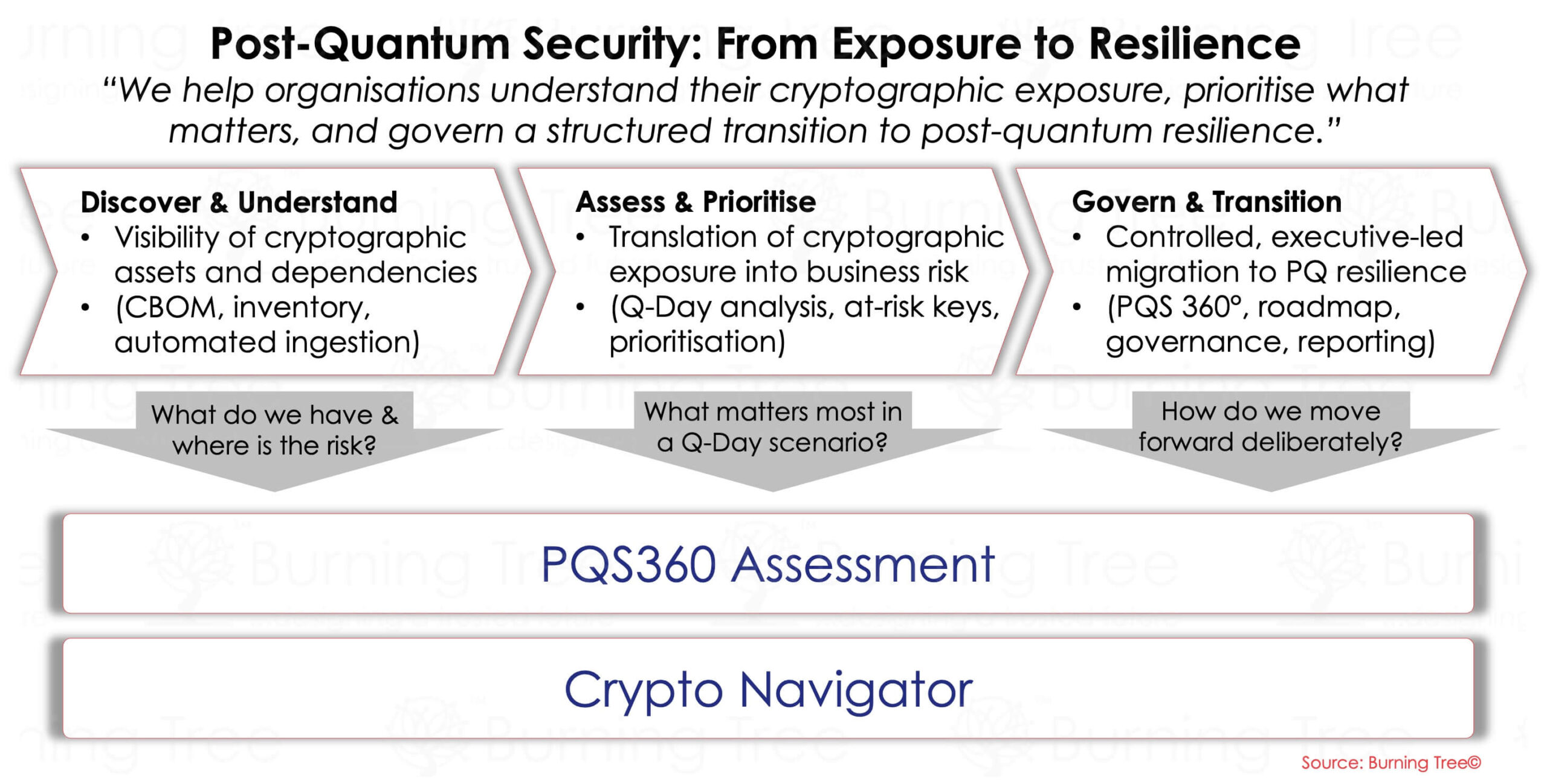
Burning Tree’s Post-Quantum Security (PQS) solution helps organisations understand their exposure, assess readiness, and build a practical, proportionate roadmap to remain secure in a post-quantum era.
Our focus is not on hype or fear, but on clarity, crypto-agility, and long-term resilience.
Why Post-Quantum Security Matters Now
Many organisations assume quantum risk is a distant problem. In reality:
• Sensitive data often has a long confidentiality lifespan
• Cryptography is deeply embedded across systems, platforms, and identities
• Migration away from vulnerable algorithms will take years, not months
• Regulators and standards bodies are already moving toward PQ-readiness
Post-quantum security is not a single upgrade — it is a strategic transformation that touches identity, data protection, infrastructure, applications, and supply chains.
What Makes Burning Tree’s PQS Approach Different
Burning Tree approaches post-quantum security as a business and architectural challenge, not just a cryptographic one.
We focus on:
• Understanding where cryptography is used
• Assessing risk based on data sensitivity and lifespan
• Designing crypto-agile architectures
• Aligning PQS to identity, Zero Trust, and enterprise security strategy
Our approach ensures organisations move forward deliberately and confidently, without unnecessary disruption.
What We Assess
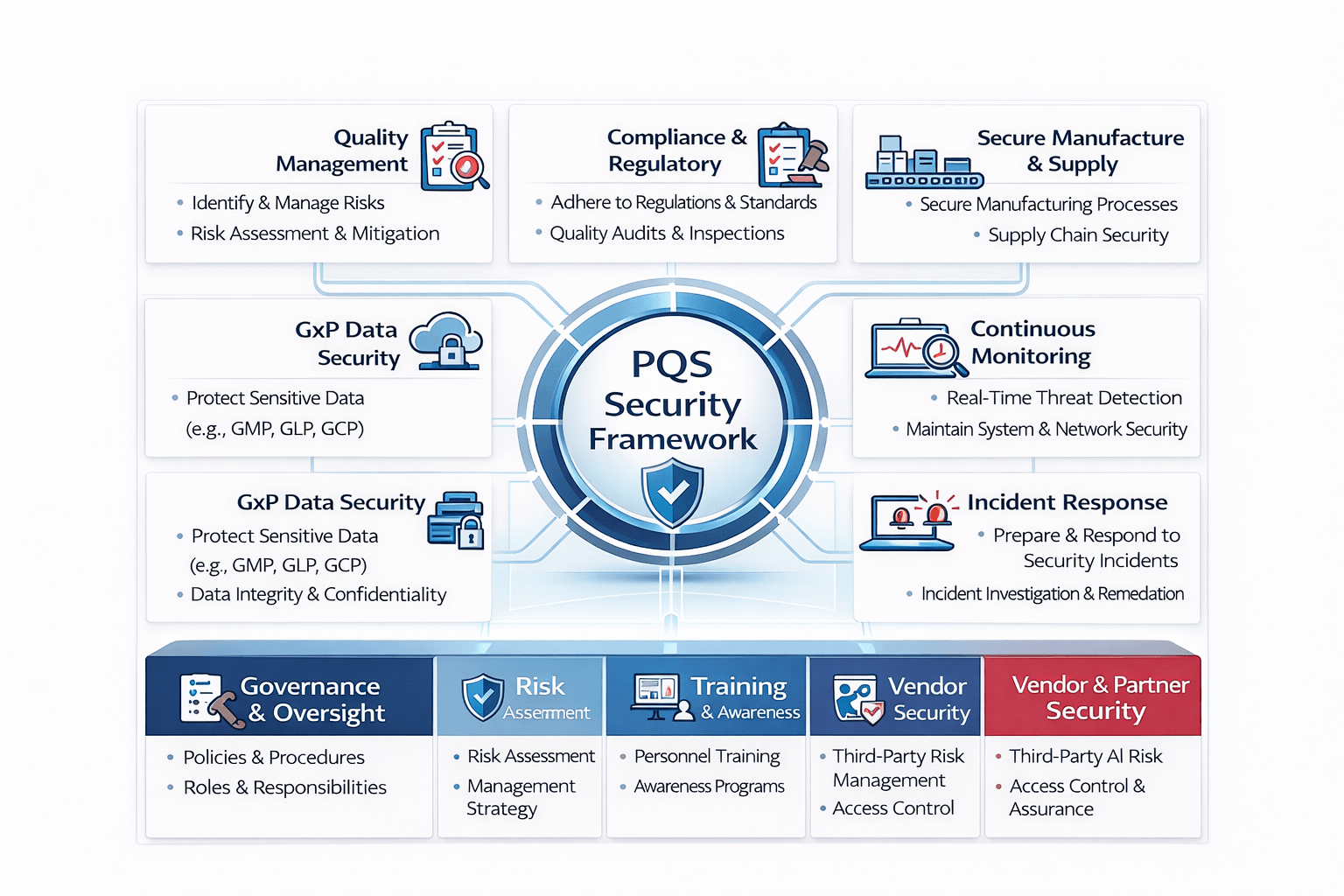
Our PQS solution begins with a structured assessment of your current environment, typically covering:
- Cryptographic Inventory & Mapping
Identification of cryptographic algorithms, protocols, certificates, keys, and dependencies across the estate. - Data Sensitivity & Lifespan Analysis
Understanding which data must remain confidential long into the future. - Identity & Authentication Dependencies
Analysis of IAM, PKI, certificates, authentication flows, and trust models. - Application & Infrastructure Exposure
Review of cloud, on-prem, third-party, and embedded cryptography. - Third-Party & Supply Chain Risk
Assessment of vendor and partner readiness for post-quantum migration. - Standards & Regulatory Alignment
Review against emerging guidance (e.g. NIST PQC, industry and government direction).
PQS Maturity & Readiness Framework
Burning Tree evaluates post-quantum readiness across defined maturity stages, from:
• Awareness & Discovery
• Risk Understanding & Prioritisation
• Crypto-Agility Design
• Migration Planning & Testing
• Operational Readiness & Governance
This allows organisations to understand where they are, what matters most, and what a realistic target state looks like.
From Assessment to Action
Our PQS solution delivers clear, actionable outcomes:
• Executive-level risk briefing
• Post-Quantum Readiness Assessment & Heatmap
• Cryptographic Risk Prioritisation
• Crypto-Agility Architecture Recommendations
• Phased PQS Roadmap aligned to business change
• Policy & Governance Guidance
• Integration with IAM, Zero Trust, and Security Architecture
Where appropriate, we support proof-of-concept testing and vendor engagement — always in a vendor-neutral role.
Explore more on Post-Quantum Security through insights from our experts, including blogs, articles, and in-depth research—helping you stay ahead of emerging cryptographic risks and evolving industry guidance.
